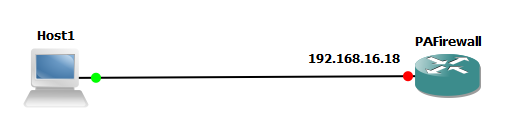
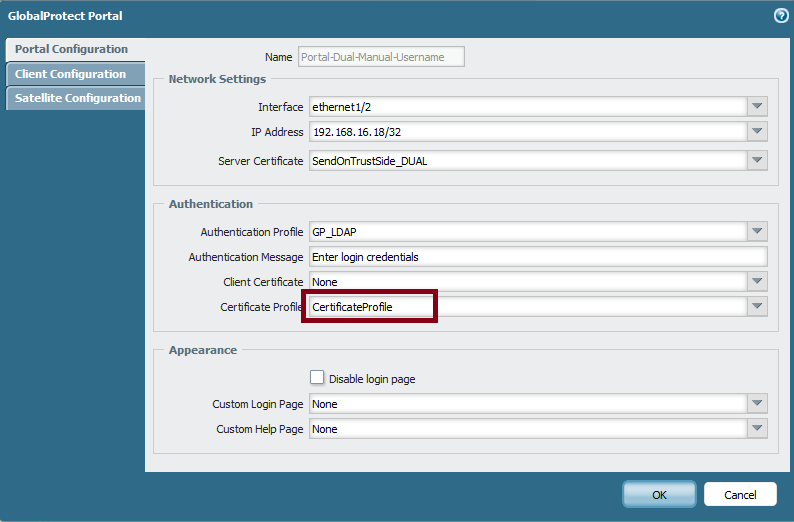
The portal has IP address of 192.168.16.18
Following are the additional step that has to be done for configuring DUAL factor authentication. Client will provide password and Certificate to authenticate himself with portal and/or gateway. In this example firewall is used to create root CA certificate, Client Certificate.
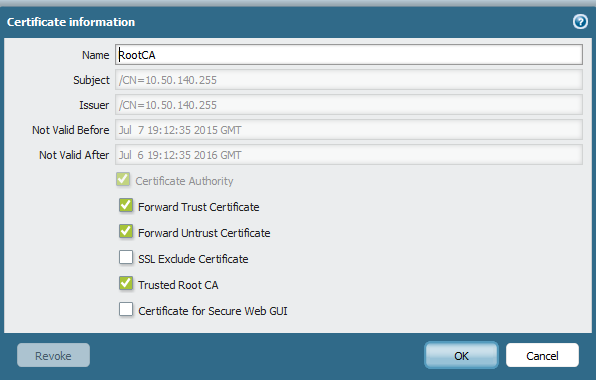
1) Create a Root CA certificate on Firewall
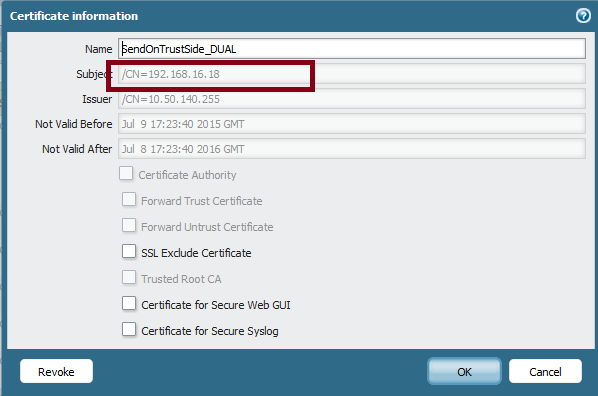
2. Create one certificate for GlobalProtect Portal and Gateway
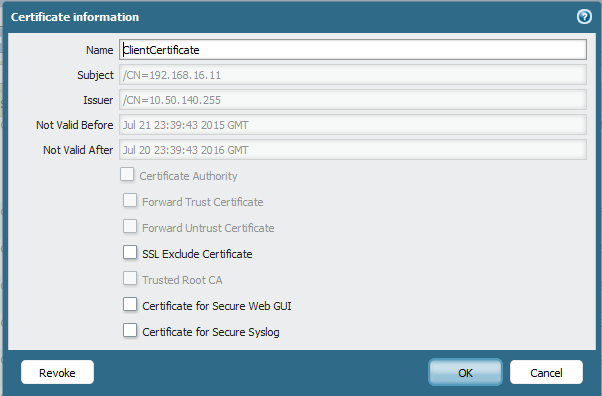
3. Use your enterprise PKI or a public CA to issue a unique client certificate to each GlobalProtect user. All clients can share the same certificate or can have their own individual certificate.
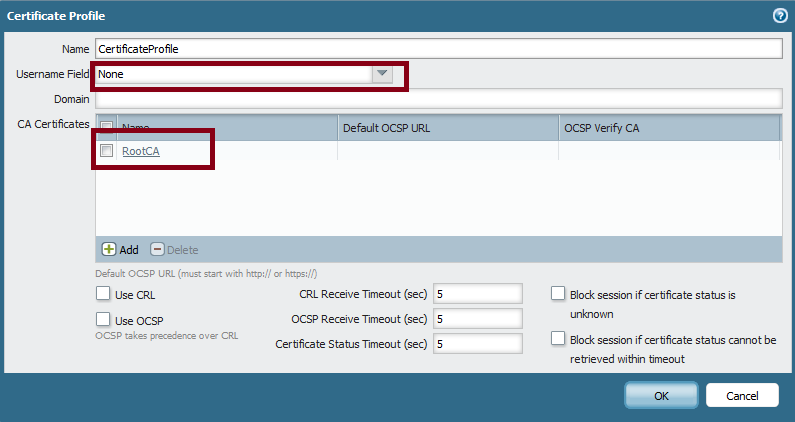
3. Create a Certification profile for Client authentication and call the Root CA.
If the certificate profile does not specify a username field (Username Field set to "None"), the client certificate does not need to have a username. In this case, the client must provide the username when authenticating against the authentication profile.
If the certificate profile specifies a username field, the certificate that the client presents must contain a username in the corresponding field. For example, if the certificate profile specifies that the username field is subject, the certificate presented by the client must contain a value in the common-name field or authentication will fail. In addition, when the username field is required, the value from the username field of the certificate will automatically be populated as the username when the user attempts to enter credentials
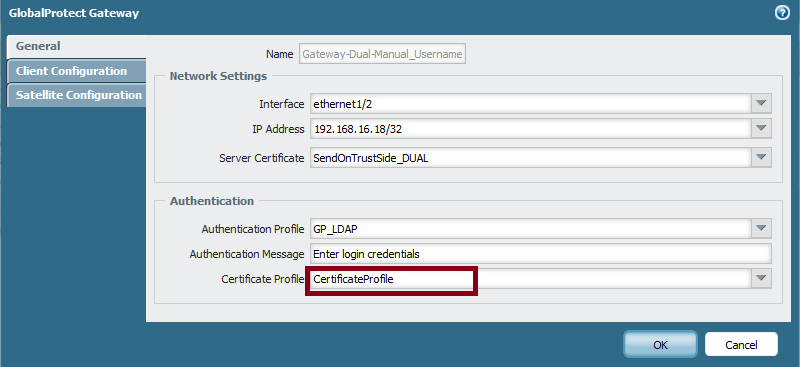
4. Call that certificate profile under the Portal and Gateway configuration
5. Install the certificate on the client machine. If the certificate is not installed, the following error message will be seen:
