Sizing for the VM-Series on Microsoft Azure
When sizing your VM for VM-Series on Azure, there are many factors to consider including your projected throughput (VM-Series model), the deployment type (e.g., VNET to VNET, hybrid cloud using IPSec or Internet facing) and number of network interfaces (NIC). This article will cover the factors below impact your Azure VM size:
- VM-Series model (VM-100, -200, -300, -500, -700 or -1000HV)
- Azure VM size: CPU cores, memory and network interfaces
- Network performance of the Azure VM instance type
VM-Series licensing and model choice
The VM-Series on Azure supports consumption-based licensing via the Azure Marketplace, bring your own license and the VM-Series Enterprise Licensing Agreement, or ELA.
- Consumption-based licensing: Use your Azure Management Console to purchase and deploy VM-Series hourly subscription bundles directly from the Azure Marketplace.
- Bundle 1 contents: VM-300 firewall license, Threat Prevention (inclusive of IPS, AV, malware prevention) subscription and Premium Support (written and spoken English only).
- Bundle 2 contents: VM-300 firewall license, Threat Prevention (inclusive of IPS, AV, malware prevention), WildFire, URL Filtering and GlobalProtect subscriptions, and Premium Support (written and spoken English only).
- Bring your own license: You can purchase any one of the VM-Series models, along with the associated subscriptions and support, via normal Palo Alto Networks channels and then deploy via a license authorization code through your Azure Management Console.
- VM-Series ELA: For large-scale deployments on Azure or across multiple virtualization environments, the VM-Series ELA allows you to forecast, and purchase upfront, the VM-Series firewalls to be deployed over a one- or three-year period. The VM-Series ELA gives you a single license authorization code used for the life of the term, providing predictable security spend and simplifying the licensing process by establishing a single start and end date for all VM-Series licenses and subscriptions. Each VM-Series ELA includes a VM-Series firewall, subscriptions for Threat Prevention, URL Filtering, WildFire, and GlobalProtect Gateway, plus unlimited Panorama virtual machine licenses and support.
Review the licensing options article to help guide your selection. The VM-Series model you choose for a BYOL deployment should be based on the capacities of the models and deployment use case. Use the data sheets , product comparison tool and documentation for selecting the model.
Azure Virtual Machine size choice
Performance of VM-Series is dependent on capabilities of the Azure Virtual Machine types. Larger VM types have more cores, more memory, more network interfaces, and better network performance in terms of throughput, latency and packets per second. Larger VM sizes can be used with smaller VM-Series models. If a larger VM size is used for the VM-Series, only the max CPU cores and memory shown in the table will be fully utilized, but it can take advantage of the faster network performance provided by Azure.
VM-Series for Azure supports the following types of Standard Azure Virtual Machine types.
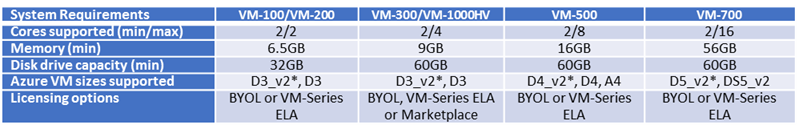
Table 1: Supported Azure VM sizes based on the CPU cores and memory required for each VM-Series model.
* Refers to recommended size based on CPU cores, memory, and number of network interfaces.
Note: The VM-50 model is not supported on Azure.
In most common usage scenarios D3 or D3_v2, and D4 or D4_v2 are the recommended VM sizes on Azure. This is based on the Azure infrastructure costs, VM-Series performance, Azure network bandwidth and required number of NICs. These sizes also allow for more granular scale out scenarios when the VM-Series is deployed behind load balancers such as Azure Application Gateway for protecting Internet facing web services, or using Azure Load Balancer for all types of applications.
Common deployment scenarios for VM-Series on Azure require only 4 NIC’s: Management, Untrust, Trust and an additional interface for optional uses such as DMZ. This allows for zone based policies north-south, i.e. in-out of the Azure virtual network (VNET), and intra-zone polices, per subnet or IP range, on the trust interface. Additional interfaces may help segment and protect additional areas like DMZ. Untrust implies external to VNET, either an on-premises network or Internet facing, while Trust refers to the side of VNET on the inside, say private subnets where applications are hosted.
In traditional networking, both physical world and virtualized, virtual appliances like firewalls use one interface for management and rest are for dataplane. The additional dataplane interfaces are used to connect to multiple networks such as Internet facing, untrust, DMZ, trust, web front end, application layer and database. This allows for protecting both north-south, i.e. entering and leaving a VNET, and east-west, i.e. between subnets or application tiers inside a VNET. Azure’s networking provides user-defined route (UDR) tables to force traffic through the firewall. These rules are set on a per subnet basis and send all outbound traffic of the subnet to a specific IP address of the firewall. This means that the firewall does not need to be part of each subnet that it is protecting and the Trust interface can send/receive traffic from all internal/private subnets.
Changing the VM size
The safest method of choosing an Azure instance type for the VM-Series is to use the guidance above and then pad your result a bit. Run the firewall and monitor the performance for a few weeks. Use a combination of Azure monitoring tools and PAN-OS dashboard to monitor the real-world performance of the firewall. After you have real data, you can resize the VM size lower or higher as needed using the Azure Portal. You will need to stop the VM to change the size.
Note: Azure VM’s include a local/temporary disk that is meant to be used as swap disk and is not for persistent storage. VM-Series logs are stored on the OS disk VHD in the Azure storage account used at time of deployment; swap disk is not used by VM-Series. For additional log storage you can attach an additional data disk VHD.