NOTE: The Palo Alto Networks supports only tunnel mode for IPSec VPN. The transport mode is not supported for IPSec VPN.
Step 1
Go to
Network >Interface > Tunnel tab, click
Add to create a new tunnel interface and assign the following parameters:
- Name: tunnel.1
- Virtual router: (select the virtual router you would like your tunnel interface to reside)
- Security Zone:(configure a new zone for the tunnel interface for more granular control of traffic ingress/egressing the tunnel)
NOTE: If the tunnel interface is in a zone different from the zone where the traffic will originate or depart, then a policy is required to allow the traffic to flow from the source zone to the zone containing the tunnel interface.
Configuring ip-address on the tunnel interface is optional. One needs IP-address if you intend to run dynamic routing protocols over the tunnel interface.
Step 2
- Go to Network > Network Profiles > IKE Crypto ,
- click Add and define the IKE Crypto profile (IKEv1 Phase-1) parameters.
- Name does not matter, it be whatever you like.
- These parameters should match on the remote firewall for the IKE Phase-1 negotiation to be successful.
Step 3
- Go to Network > Network Profiles > IKE Gateway to configure the IKE Phase-1 Gateway.
- Version: There are options for the Version where you can select IKEv1 only mode, IKEv2 only mode or IKEv2 preferred mode.
Select the IKE version that the gateway supports and must agree to use with the peer gateway. IKEv2 preferred mode causes the gateway to negotiate for IKEv2, and if the peer also supports IKEv2, that is what they will use. Otherwise, the gateway falls back to IKEv1.
- Interface: The external interface connected to the internet.
- Local and Peer Identification: Defines the format and identification of the local/peer gateway, which are used with the pre-shared key for both IKEv1 phase 1 SA and IKEv2 SA establishment.
Choose one of the following types and enter the value: FQDN (hostname), IP address, KEYID (binary format ID string in HEX), or User FQDN (email address). If one does not specify the value, the gateway will use the local/peer IP address as the local/Peer identification value.
Click on Advanced Options tab:
- Enable Passive Mode - The firewall to be in responder only mode. The firewall will only respond to IKE connections and never initiate them.
- Exchange Mode - The device can accept both main mode and aggressive mode negotiation requests; however, whenever possible, it initiates negotiation and allows exchanges in main mode
Step 4
- Under Network > Network Profiles > IPSec Crypto , click Add to create a new Profile, define the IPSec Crypto profile to specify protocols and algorithms for identification, authentication, and encryption in VPN tunnels based on IPSec SA negotiation (IKEv1 Phase-2).
- These parameters should match on the remote firewall for the IKE Phase-2 negotiation to be successful.
Step 5
- Under Network > IPSec Tunnels, click Add to create a new IPSec Tunnel.
- In the General window use the Tunnel Interface, the IKE Gateway and IPSec Crypto Profile from above to set up the parameters to establish IPSec VPN tunnels between firewalls.
NOTE: If the other side of the tunnel is a peer that supports policy-based VPN, you must define Proxy IDs
When configuring an IPSec Tunnel Proxy-ID configuration to identify local and remote IP networks for traffic that is NATed, the Proxy-ID configuration for the IPSec Tunnel must be configured with the Post-NAT IP network information, because the Proxy-ID information defines the networks that will be allowed through the tunnel on both sides for the IPSec configuration.
Step 6
- Under Network > Virtual Routers, click on your Virtual router profile, then click Static Routes,
- Add a new route for the network that is behind the other VPN endpoint. Use the proper Tunnel Interface.
- Click OK when done.
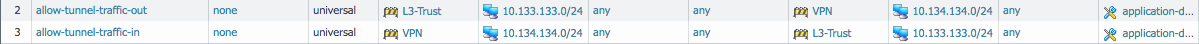
Step 7
Configure the required security rules/policies
Allow IKE negotiation and IPSec/ESP packets. By default the IKE negotiation and IPSec/ESP packets would be allowed via the intrazone default allow.
If you wish to have more granular control, you could specifically allow the required traffic and deny the rest.
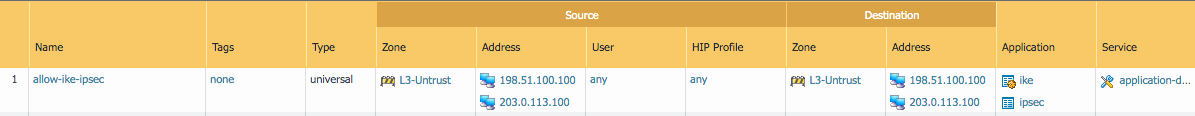
Allow incoming and outgoing traffic through the tunnel. If you require granular control of incoming and outgoing traffic, you may create separate rules for each direction.
Step 8
Commit the configuration.
NOTE:
The tunnel comes up only when there is interesting traffic destined to the tunnel.
To manually initiate the tunnel, check the status and clear tunnels refer to:
How to check Status, Clear, Restore, and Monitor an IPSEC VPN Tunnel