How to resolve improper mac addresses used on excluded GlobalProtect traffic
5638
Created On 04/29/22 21:56 PM - Last Modified 05/29/25 03:23 AM
Objective
To identify and resolve improper mac addresses used on excluded GlobalProtect traffic.
Environment
- GlobalProtect (GP) App 5.1+ using domain-based exclusion
- Windows hosts configured with Routing & Remote Access Service (RRAS)
- Wireshark
Procedure
To validate if you're encountering the issue, you can complete the following steps:
- Install the Wireshark app.
- Connect to GP and enable dump level logging by navigating to the App's menu > Settings > Troubleshooting > Logging Level: Dump and exit the app.
- Launch Wireshark and enable capturing on both the GP and physical adapters (you can verify their naming convention by using command prompt as shown below):
- Navigate to the url that's unreachable while connected to the GP VPN and notate the timestamp.
- After replicating the issue stop the Wireshark capture and then generate the GP logs by navigating to Menu > Settings > Troubleshooting > Collect Logs.
- Verify the App properly excluded the domain traffic by reviewing the GPS log file for similar logs shown to the ones below:
(T15964)Dump ( 91): 04/26/22 17:09:04:899 Received DNS request for <DOMAIN NAME> with type 1 (T15964)Dump (1259): 04/26/22 17:09:04:899 Domain name <DOMAIN NAME> matches exclude single domain in hash table (T15964)Dump ( 504): 04/26/22 17:09:04:899 SP added an exclude ip <DOMAIN IP>, port 0, ttl 60 for domain <DOMAIN NAME>, original ttl=60, infinite ttl=no (T15964)Dump ( 504): 04/26/22 17:09:04:899 SP added an exclude ip <DOMAIN IP>, port 0, ttl 60 for domain <DOMAIN NAME>, original ttl=60, infinite ttl=no (T15964)Dump ( 536): 04/26/22 17:09:04:899 call SPSetParameters to set 2 exclude IPs (T15964)Dump ( 264): 04/26/22 17:09:04:899 original iTimeOut=60, new iTimeOut=120 (T15964)Dump ( 268): 04/26/22 17:09:04:899 iTimeOut=120 (T15964)Dump ( 873): 04/26/22 17:09:04:899 ST,argc=6 (T15964)Dump (2088): 04/26/22 17:09:04:899 ST,shouldCacheCommand return false (T15964)Dump (1351): 04/26/22 17:09:04:899 ST,remote ip address is <DOMAIN IP>, port=0, bind local address is <PHY ADAPTER IP> (T15964)Dump ( 248): 04/26/22 17:09:04:899 ST,create file to \\.\symgpproxy success, file handle is 0000000000000B14 (T15964)Dump (1383): 04/26/22 17:09:04:899 ST,new domain port is 0, 5 ip set (T15964)Dump ( 262): 04/26/22 17:09:04:899 ST,WriteFile return 0 (T15964)Dump ( 265): 04/26/22 17:09:04:899 ST,lasterror is 997 (T15964)Dump ( 267): 04/26/22 17:09:04:899 ST,lasterror is ERROR_IO_PENDING (T15964)Dump ( 269): 04/26/22 17:09:04:899 ST,write success (T15964)Dump (1402): 04/26/22 17:09:04:899 ST,create time task 6, delay 120 seconds (T15964)Dump (1411): 04/26/22 17:09:04:899 ST,task for <DOMAIN IP> already exist, increase counter (T15964)Dump ( 283): 04/26/22 17:09:04:899 ST,close file handle 0000000000000B14 (T15964)Dump ( 264): 04/26/22 17:09:04:899 original iTimeOut=60, new iTimeOut=120 (T15964)Dump ( 268): 04/26/22 17:09:04:899 iTimeOut=120 (T15964)Dump ( 873): 04/26/22 17:09:04:899 ST,argc=6 (T15964)Dump (2088): 04/26/22 17:09:04:899 ST,shouldCacheCommand return false (T15964)Dump (1351): 04/26/22 17:09:04:899 ST,remote ip address is <DOMAIN IP>, port=0, bind local address is <PHY ADAPTER IP> (T15964)Dump ( 248): 04/26/22 17:09:04:899 ST,create file to \\.\symgpproxy success, file handle is 0000000000000BC0 (T15964)Dump (1383): 04/26/22 17:09:04:899 ST,new domain port is 0, 6 ip set (T15964)Dump ( 262): 04/26/22 17:09:04:900 ST,WriteFile return 0 (T15964)Dump ( 265): 04/26/22 17:09:04:900 ST,lasterror is 997 (T15964)Dump ( 267): 04/26/22 17:09:04:900 ST,lasterror is ERROR_IO_PENDING (T15964)Dump ( 269): 04/26/22 17:09:04:900 ST,write success (T15964)Dump (1402): 04/26/22 17:09:04:900 ST,create time task 7, delay 120 seconds (T15964)Dump (1411): 04/26/22 17:09:04:900 ST,task for <DOMAIN IP> already exist, increase counter (T15964)Dump ( 283): 04/26/22 17:09:04:900 ST,close file handle 0000000000000BC0
- As you continue following the logs, you should immediately encounter entries stating traffic was discarded as shown below:
(T15548)Dump (1330): 04/26/22 17:09:04:903 Received an IP packet with a non-tunnel source IP <PHY ADAPTER IP> (T15548)Dump (1553): 04/26/22 17:09:04:903 the packet received from virtual interface is discarded (T15548)Dump (1330): 04/26/22 17:09:04:905 Received an IP packet with a non-tunnel source IP <PHY ADAPTER IP> (T15548)Dump (1553): 04/26/22 17:09:04:905 the packet received from virtual interface is discarded
- Open the Wireshark capture and isolate the test traffic to notated domain using your filter of choice
Note: In our example, we used the IPs provided by the GP logs to filter for the destination traffic (ip.addr==<source/destination ip>)
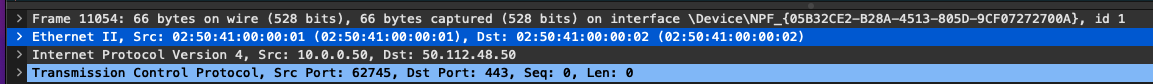
- Take note of the mac addresses used in the previous step; they should match those of the GP interface and firewall tunnel interface. You can verify this by reviewing the "ipconfig.txt" file in the GP log folder collected in Step 5.
Ethernet adapter Ethernet 3: Connection-specific DNS Suffix . : Description . . . . . . . . . . . : PANGP Virtual Ethernet Adapter Physical Address. . . . . . . . . : 02-50-41-00-00-01 DHCP Enabled. . . . . . . . . . . : No Autoconfiguration Enabled . . . . : Yes IPv4 Address. . . . . . . . . . . : <GP IP>(Preferred)
- In the same GP log folder, locate the nicdetails.txt" log file and confirm if the "Forwarding" section displays "enabled" under either the GP or local adapter(s) as shown below:
Note: The naming convention should be the same from the command prompt output listed in Step 3
Interface Ethernet 3 Parameters ---------------------------------------------- IfLuid : ethernet_32773 IfIndex : 2 State : connected Metric : 1 Link MTU : 1400 bytes Reachable Time : 42500 ms Base Reachable Time : 30000 ms Retransmission Interval : 1000 ms DAD Transmits : 3 Site Prefix Length : 0 Site Id : 1 Forwarding : enabled
- If so, you must disable the Microsoft Routing & Remote Access Service to allow the split tunneling behavior to function properly. You can find more information regarding this feature in the following Microsoft Document.