Overview
This document completely explains about RADIUS authentication with the PaloAlto Networks firewall with read only and read write access using the Cisco ACS server.
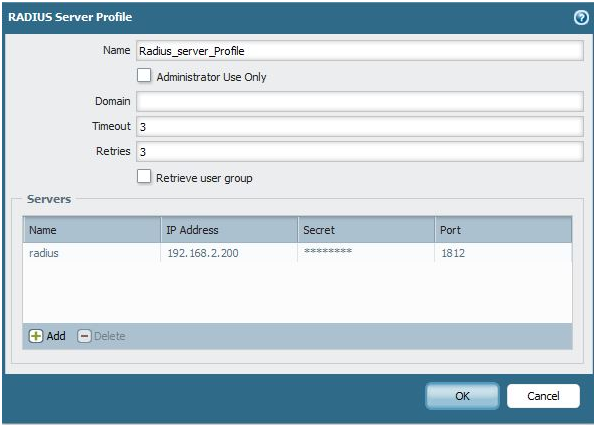
1. Inside of the WebGUI, go to Device > Server Profiles > RADIUS, Create a radius server profile, if you have secondary radius server (backup) you can add it. Make sure to Add a RADIUS name, IP address, secret, and confirm the port.
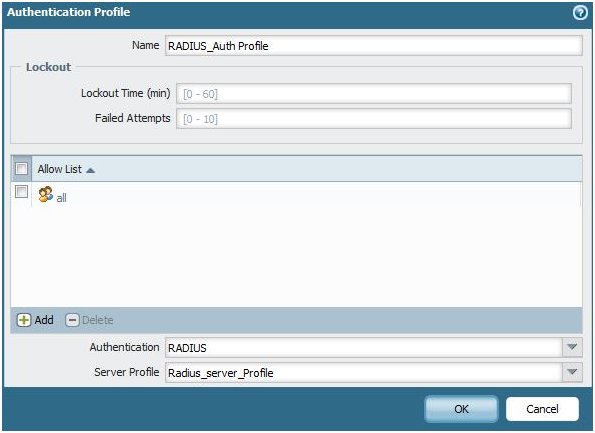
2. Next, inside Device > Authentication Profile, create a new authentication profile. Under the Allow List, be sure to leave it as "any". Because users are present in radius server we can give authorization rules under RADIUS server.
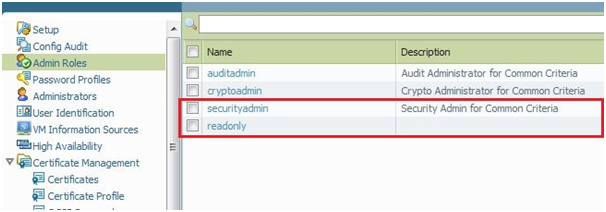
3. Now under Device > Admin Roles, by default we have 3 roles:
- auditadmin
- cryptoadmin
- securityadmin
Here we use securityadmin role for READ_WRITE access.
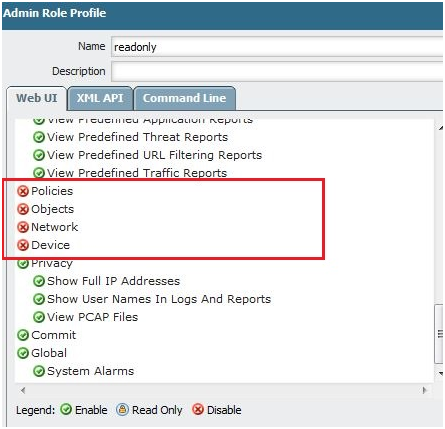
4. Create another admin role with limited access as below; here I have disabled Policies, Objects, Network, Device.
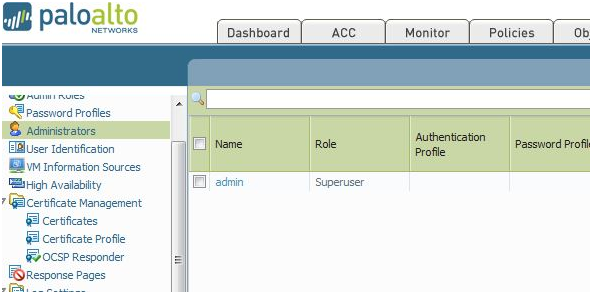
5. Under Device > Administrators, you can see there are no users defined except admin.
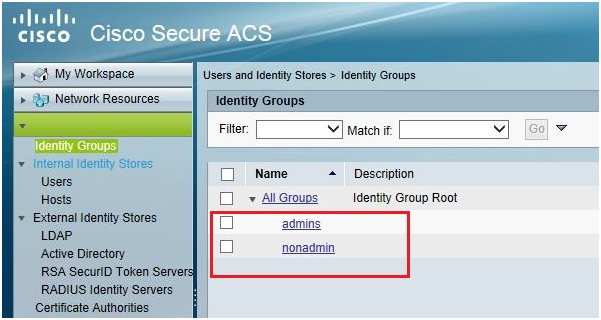
6. Configuration under Cisco Acs server:.
Inside Users and Identity Stores > Identify Groups, Create two identity groups one for admins another for nonadmin.
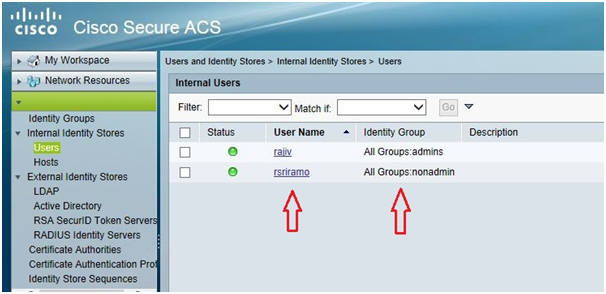
7. Inside Users and Identity Stores > Identify Groups > Users, you can create users in radius server and give them to respective identity groups. Here I have created two users which are pointed to admins and nonadmin groups.
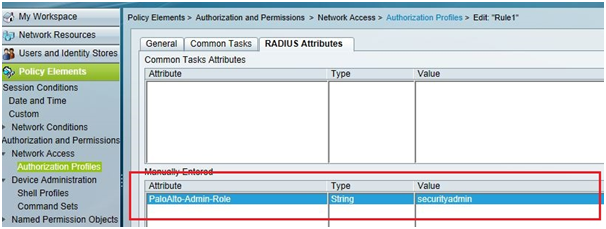
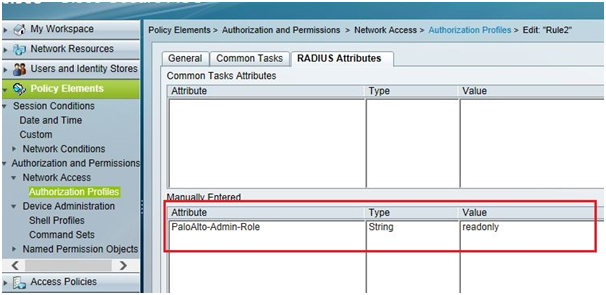
8. Inside Policy Elements > Authorization and Permissions > Network Access > Authentication Profiles, Create Two authorization profiles, one for read_only and other read_write.
Here we need to enter the name of the admin role which we created in Palo Alto Networks firewall.
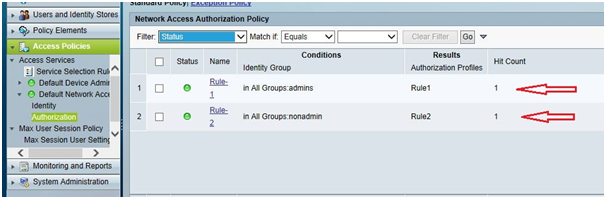
9. Now inside Access Policies > Authorization, finally create two authorization policies, one for read only and other for read write access
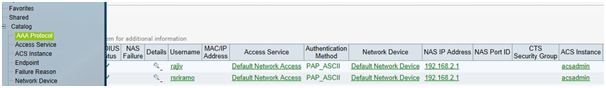
10. Here are the successful Passed authentication logs from ACS server
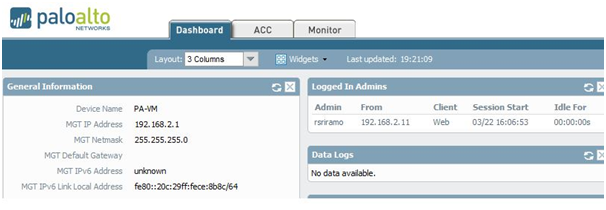
11. Read_only access to the PaloAlto Firewall looks like this:
owner: rsriramoju