SMB Traffic is Blocked and the Windows Explorer Window Hangs While Accessing a Shared Folder
Resolution
Issue
Server Message Block (SMB) traffic is blocked and the Windows Explorer window hangs while accessing a shared folder.
Cause
This can happen when there is a file blocking profile, with a block action used in a Security Rule that is matched by that session.
Details
Under Security Policies > Actions, if a session goes through the Palo Alto Networks firewall and matches a specific allow policy, according to the defined criteria, the action defined in the policy will be taken.
In the example below, the Security Policy Rule that is matched is "allow_all", which has a profile for file blocking.
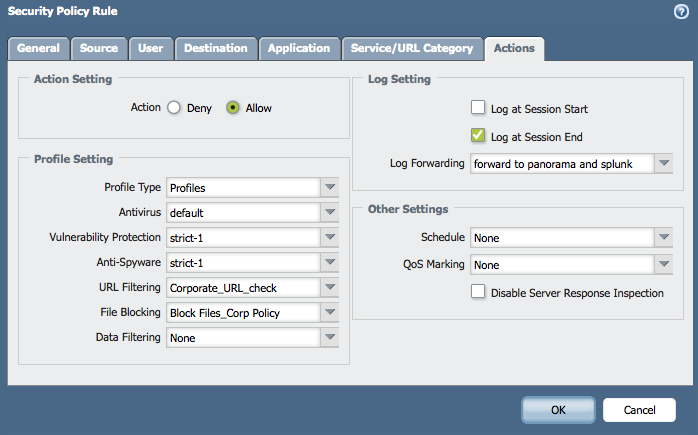
The File Blocking Profile is blocking all PE files (which includes .exe, .msi), any file in that session that matches the file type will take the session into the discard state.
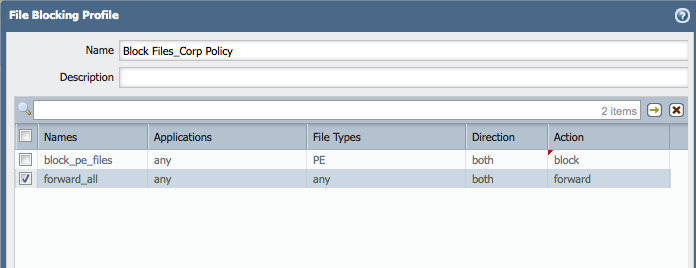
As soon as a user opens the shared folder that has .exe file in it, that session opening will go into discard state and no other files will be able to move between the machines.
> show session all filter destination 10.193.17.10
--------------------------------------------------------------------------------
ID Application State Type Flag Src[Sport]/Zone/Proto (translated IP[Port])
Vsys Dst[Dport]/Zone (translated IP[Port])
--------------------------------------------------------------------------------
152568 ms-ds-smb DISCARD FLOW NS 192.168.8.136[49158]/Trust-L3/6 (10.193.17.8[32047])
vsys1 10.193.17.10[445]/Untrust-L3 (10.193.17.10[445])
See the following example, session is set to discard state by security policy check:
> show session id 152568
Session 152568
c2s flow:
source: 192.168.8.136 [Trust-L3]
dst: 10.193.17.10
proto: 6
sport: 49158 dport: 445
state: INIT type: FLOW
src user: unknown
dst user: unknown
s2c flow:
source: 10.193.17.10 [Untrust-L3]
dst: 10.193.17.8
proto: 6
sport: 445 dport: 32047
state: INIT type: FLOW
src user: unknown
dst user: unknown
start time : Thu Apr 17 17:12:56 2014
timeout : 90 sec
total byte count(c2s) : 44292
total byte count(s2c) : 50073
layer7 packet count(c2s) : 182
layer7 packet count(s2c) : 176
vsys : vsys1
application : ms-ds-smb
rule : allow_all
session to be logged at end : True
session in session ager : False
session synced from HA peer : False
address/port translation : source + destination
nat-rule : NAT_all_inside_to_out(vsys1)
layer7 processing : completed
URL filtering enabled : True
URL category : any
session via syn-cookies : False
session terminated on host : False
session traverses tunnel : False
captive portal session : False
ingress interface : ethernet1/2
egress interface : ethernet1/1
session QoS rule : N/A (class 4)
tracker stage firewall : mitigation block cont url
As soon as the folder is opened, the SMB session will go into the discard state. If the same folder has .txt files, and if trying to copy them, it will fail because the SMB session is already discarded. This is going to happen even if there is no blocking policy for the .txt files.
The user will experience this as their Windows Explorer application hangs and does not return any results after the share folder was opened.
As shown below, the global counters confirms that information too:
> show counter global filter packet-filter yes delta yes
Global counters:
Elapsed time since last sampling: 58.678 seconds
name value rate severity category aspect description
--------------------------------------------------------------------------------
pkt_recv 1511 25 info packet pktproc Packets received
pkt_sent 349 5 info packet pktproc Packets transmitted
session_allocated 2 0 info session resource Sessions allocated
session_installed 2 0 info session resource Sessions installed
session_discard 4 0 info session resource Session set to discard by security policy check
flow_fwd_mtu_exceeded 21 0 info flow forward Packets lengths exceeded MTU
flow_ipfrag_frag 42 0 info flow ipfrag IP fragments transmitted
flow_host_pkt_xmt 1248 21 info flow mgmt Packets transmitted to control plane
flow_host_vardata_rate_limit_ok 1227 20 info flow mgmt Host vardata not sent: rate limit ok
appid_ident_by_dport 1 0 info appid pktproc Application identified by L4 dport
appid_proc 2 0 info appid pktproc The number of packets processed by Application identification
appid_use_dfa_1 2 0 info appid pktproc The number of packets using the second DFA table
appid_skip_terminal 2 0 info appid pktproc The dfa result is terminal
nat_dynamic_port_xlat 2 0 info nat resource The total number of dynamic_ip_port NAT translate called
dfa_sw 326 5 info dfa pktproc The total number of dfa match using software
ctd_run_pattern_match_failure 2 0 info ctd pktproc Run pattern match failure
aho_sw 507 8 info aho pktproc The total usage of software for AHO
ctd_appid_reassign 5 0 info ctd pktproc appid was changed
ctd_pkt_slowpath 318 5 info ctd pktproc Packets processed by slowpath
ctd_detector_discard 2 0 info ctd pktproc session discarded by detector
log_pkt_diag_us 23585 401 info log system Time (us) spend on writing packet-diag logs
--------------------------------------------------------------------------------
Total counters shown: 21
--------------------------------------------------------------------------------
Resolution
This is expected behavior because of the nature of the SMB. If there is a Security Rule with a block profile attached to it for SMB sessions, it is best to not mix file types that are supposed to be blocked, with a policy with allowed files.
owner: ialeksov