-
Requesting the certificate
Depending on which PAN-OS version is installed on the firewall, a private key and CSR may need to be generated on a third-party program such as OpenSSL.
If using PAN-OS 7.1 and above, refer to How to Generate a CSR(Certificate Signing Request) and Import the Signed Certificate
- Creating the combination certificate
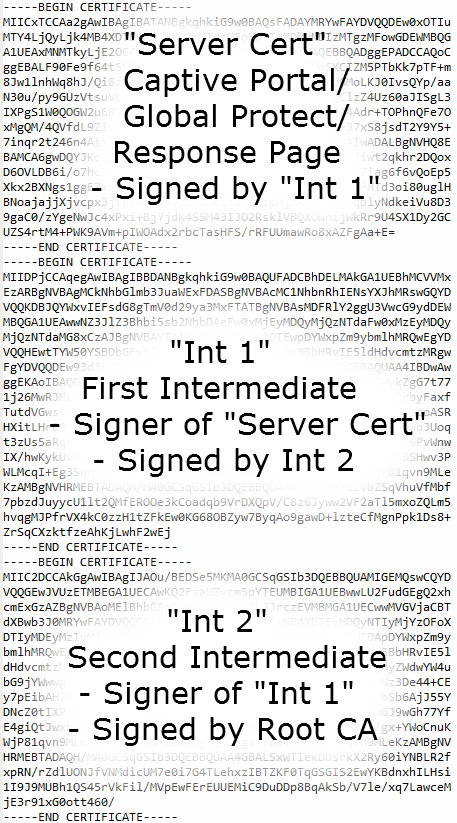
When a certificate is not signed by the Root CA, the intermediate CAs should be sent to clients in case those clients do not have the intermediate CAs in their trusted key store already. To do that, a combination certificate that consists of the signed certificate (CP, GP, and so on), followed by the intermediate CAs. The image below shows two, but the same process is valid for only one intermediate CA or several.
To get each of these certificates:
- Open the "Server Cert" file sent by the CA.
- In Windows, the certificate dialog box has three tabs: General, Details, and Certification Path.
- Click the Certification Path and click the certificate one step above the bottom.
- Open that certificate and click the Details tab, then Copy To File.
- Save the file as a Base-64 encoded X.509 (.CER) formatted certificate.
- Do the same for all certificates in the chain except the top (Root).
- Open each certificate.CER file in a plain-text editor (such as Notepad).
- Paste each certificate end-to-end, with the Server Cert on top and each signer below that.
- Save the file as a ".TXT" or ".CER" file
Note: The name of the file cannot contain spaces, as this may cause the import to fail.
- Importing the Certificate
Take the combined certificate and import it on the firewall.
Workaround
In the event that you can not generate a new CSR, but still need to export a certificate, please try these steps:
- Export the current Certificate on the Firewall, PEM format, and Private key exported.
- Open the cert in a Text editor.
- Separate the public key from the private key in two separate text files (being careful not to add any spaces).
- Save the private key text file and keep it aside.
- Edit the file where the public key is and have the public key at the top and add the intermediate CA below it as in the url shared, and save the file.
- Delete the certificate already on the firewall.
- Import the private key with the edited certificate.