What is QUIC?
QUIC (Quick UDP Internet Connections, pronounced quick) is an experimental transport layer network protocol developed by Google. QUIC supports a set of multiplexed connections between two endpoints over User Datagram Protocol (UDP), and was designed to provide security protection equivalent to TLS/SSL, along with reduced connection and transport latency, and bandwidth estimation in each direction to avoid congestion. QUIC's main goal is to optimize connection-oriented web applications currently using TCP. An experimental implementation is being put in place in Chrome by a team of engineers at Google.
What happens if QUIC is not blocked?
Chrome browsers have the QUIC protocol enabled by default. When users try to access Google applications using the Chrome browser, a session to a Google server is established using the QUIC protocol instead of TLS/SSL. QUIC is an experimental protocol at its early stages of development, and it uses proprietery encryption methods. If security policy is in place to whitelist QUIC App-ID, and if the user uses Google chrome browser to access Google applications, all those sessions will be identified as QUIC application by the Palo Alto Networks firewall's App-ID engine. Visibility and Control of Google applications is lost with whitelisting the QUIC App-ID.
Our recommendations:
Palo Alto Networks recommends creating a security policy in the firewall to block the QUIC application. With the QUIC traffic getting blocked by the Firewall, the Chrome browser will fall back to using traditional TLS/SSL. Note that this will not cause the user to lose any functionality on their browser. Firewall gains better visibility and control of Google applications with or without the SSL decryption enabled.
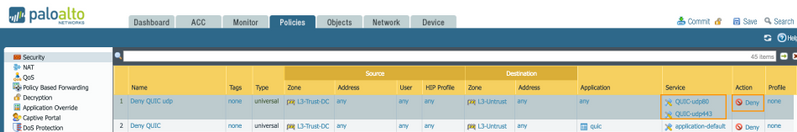
Security policy that denies QUIC App:
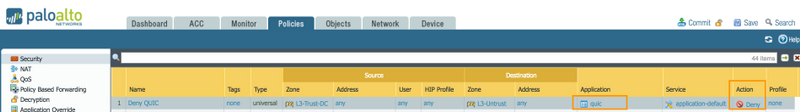
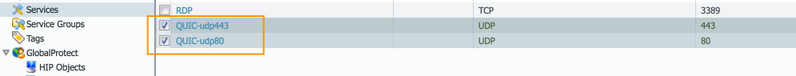
With the most recent version of the browser Chrome, Google updated their experimental protocol QUIC, which caused the "quic" App-ID to be misidentified as "unknown-udp". Palo Alto Networks released additional coverage for the "quic" App-ID to include the changes made by Google. With Google making changes to their protocol, we recommend creating additional security policy to block QUIC UDP traffic (UDP/443 and UDP/80).