Any/Any/Deny Security Rule Changes Default Behavior
Resolution
Overview
All Palo Alto Networks firewalls have two implicit Security Rules:
- Deny cross-zone traffic
- Allow same-zone traffic
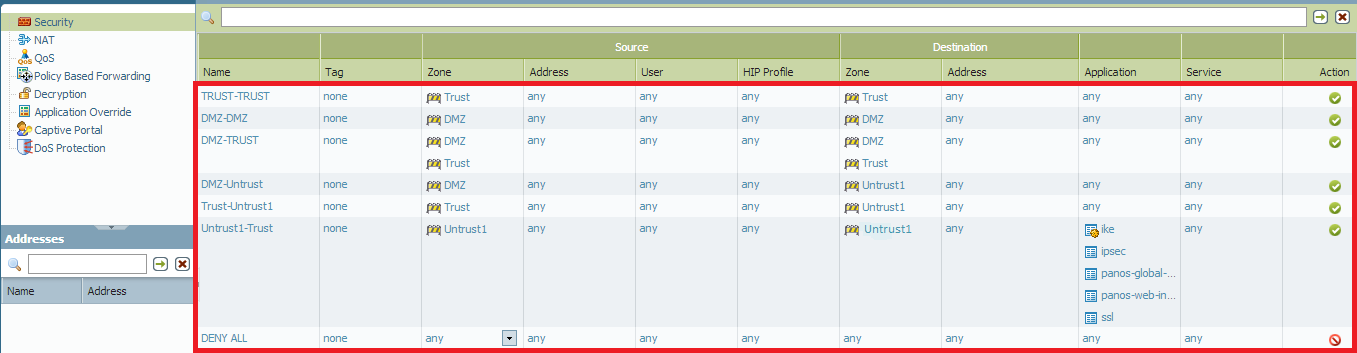
The default rules are applied unless there is a defined rule that allows traffic to pass between two zones. Traffic that hit the default rules are not logged. Some users have found that by adding a Deny All rule at the end of the list that drops all traffic from "any zone" to "any zone" they can now see traffic log entries for dropped packets. When this "deny all" rule is applied, it often has the unwanted behavior of dropping “same zone” traffic which is allowed by default. Traffic starting on the trust zone and ending on the trust zone matches the Any/Any zones of the deny rule. The end result is that SSL VPN, BGP, IPSEC and any other protocol or traffic that receives and replies on the same zone will no longer pass traffic.
With GlobalProtect, an Any/Any/Deny rule may cause the following symptoms:
- GlobalProtect (GP) clients would not connect since their connection would be from Untrust Zone to the Untrust Zone and be blocked by the Any/Any/Deny rule.
- Connectivity to internal services on same zone as GlobalProtect would not operate without a policy to allow same zone. The same connectivity with cross zone traffic if there was no policy for cross zone traffic.
The following is an example of Any/Any/Deny with SSL VPN:
The public interface of a virtual router is providing internet access and terminating SSL VPN traffic. This interface is part of a zone named UNTRUST. All SSL VPN connections would ingress the interface from the UNTRUST interface and the response would egress the UNTRUST interface.
To make this work as intended, the last two rules are shown in the example:
If you need routing protocols or other traffic to communicate on the same zone, then you may need to add additional rules:
To test default policy logging, run the following CLI command:
> set system setting logging default-policy-logging <value>
where <value> is 0-300
owner: panagent