Note: Users do not have to enter their credentials. Windows credentials will be taken for authentication.
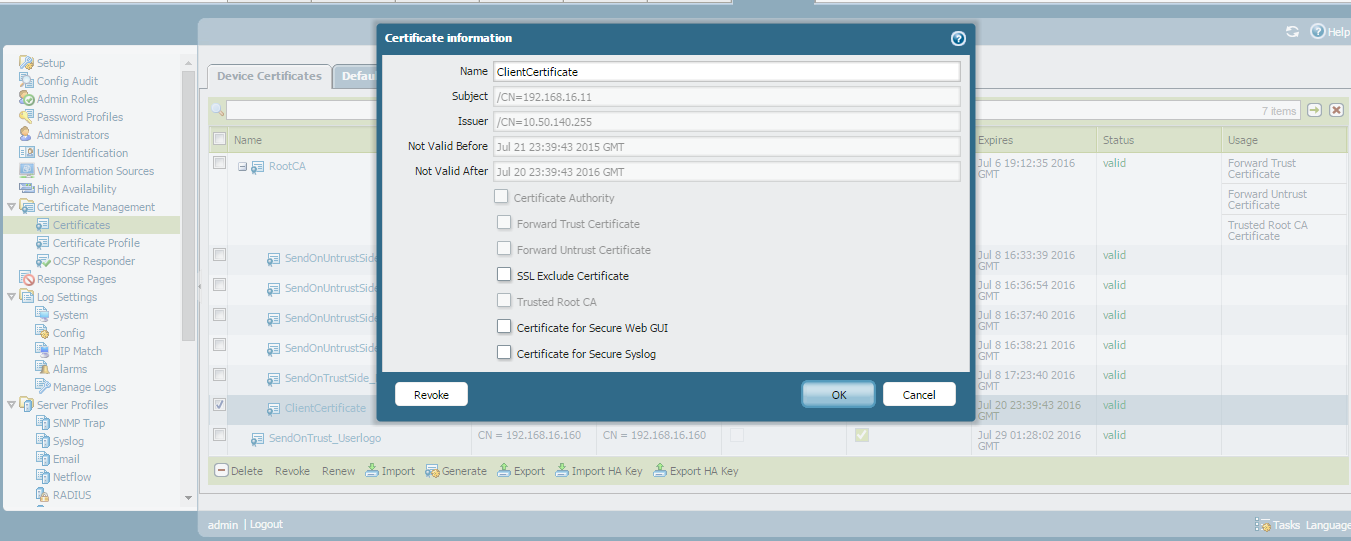
Step 1. Get a CA certificate on the Palo Alto Networks firewall or create a CA on the device itself.
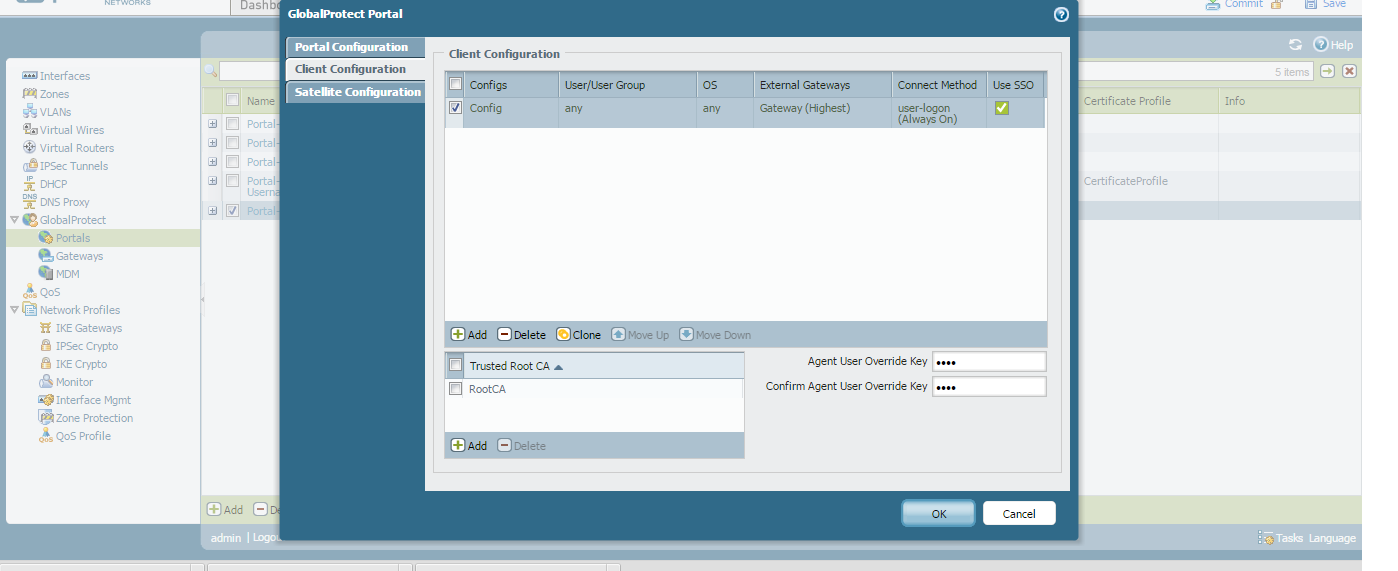
Root CA
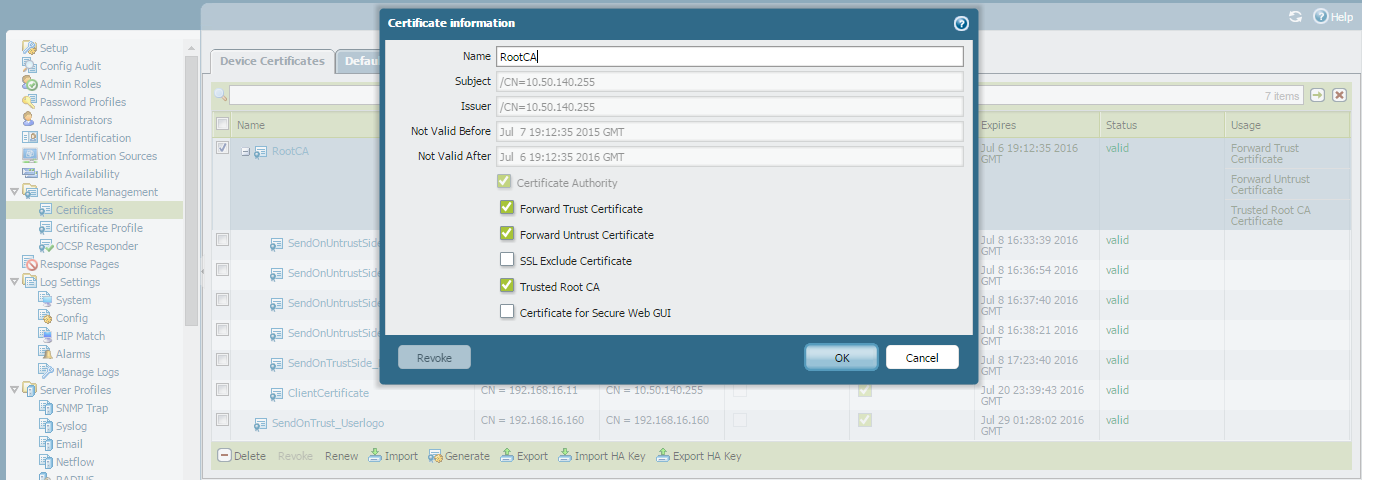
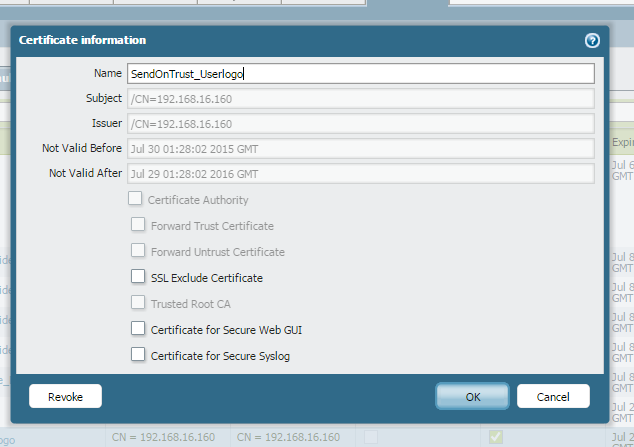
GP Certificate: This certificate will be forwarded by the portal and gateway to the end hosts.
Step 2. Create a client certificate on the Palo Alto Networks firewall. The root of this certificate should be the CA created in Step 1. This certificate has to be installed on the client systems.
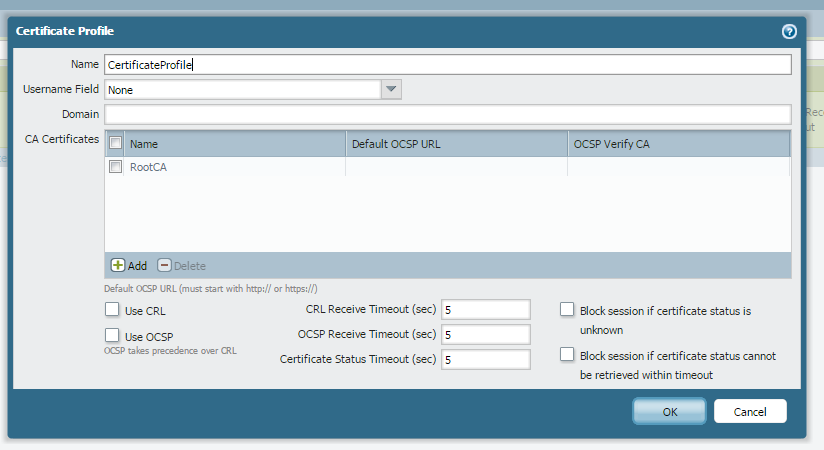
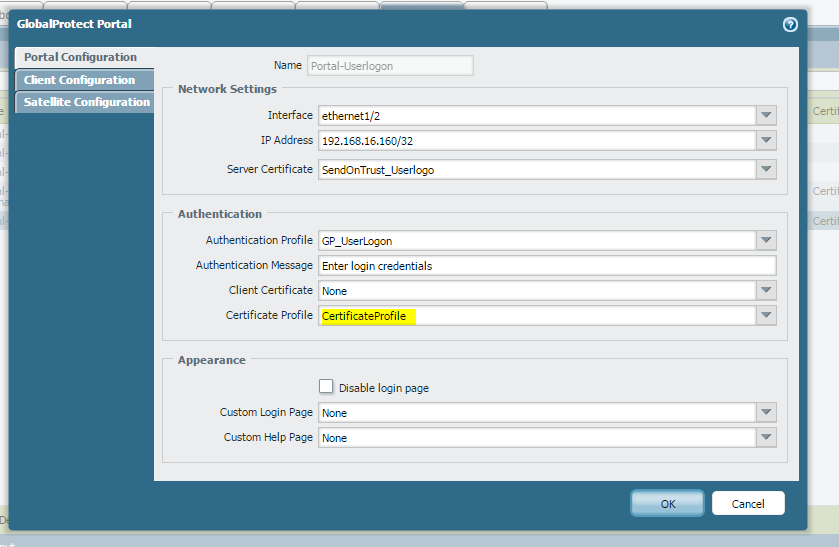
Step 3. Create a certificate profile called the ROOT CA created in Step 1.
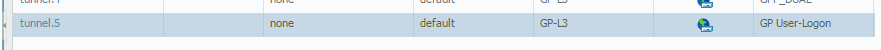
Step 4. Create a tunnel interface and assign it a specific zone and virtual router.
Step 5. Configure the Authentication profile to authenticate with domain controller.
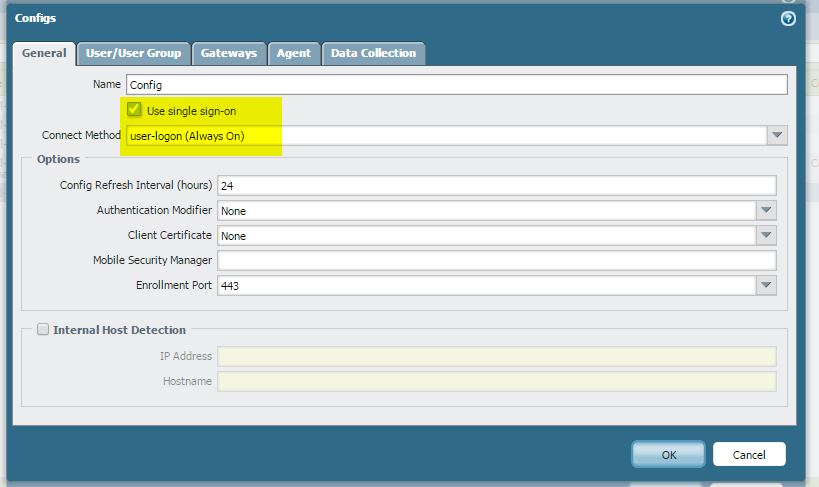
Step 6. Configure Portal. Make sure you select connect method as user-logon and select user single sign-on option.
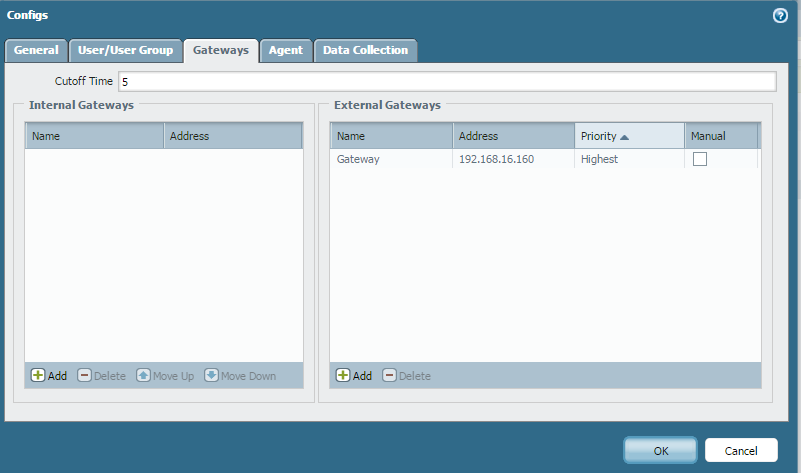
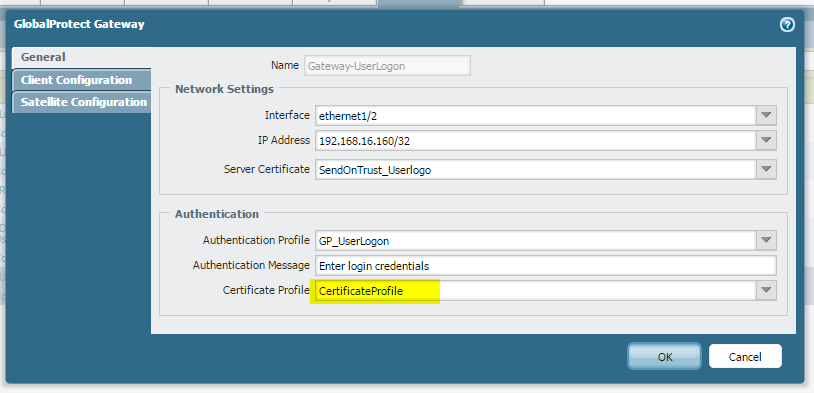
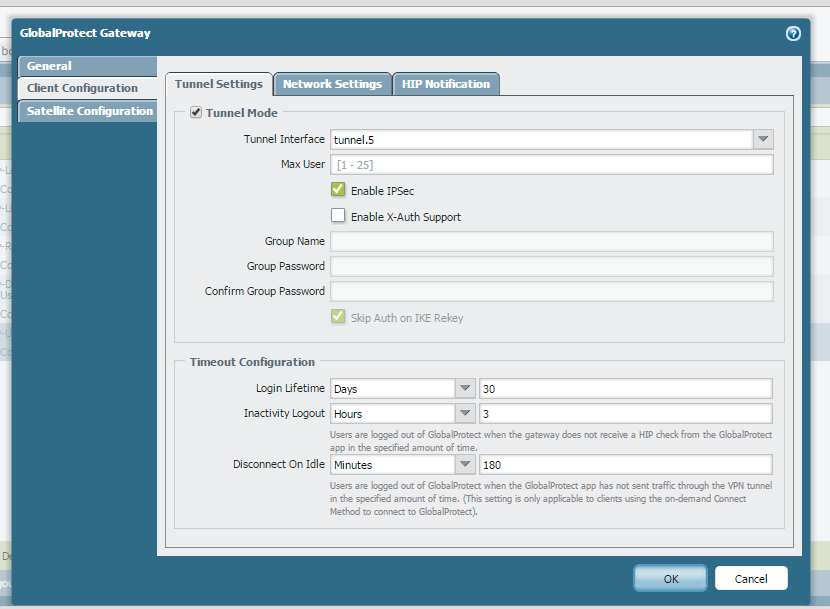
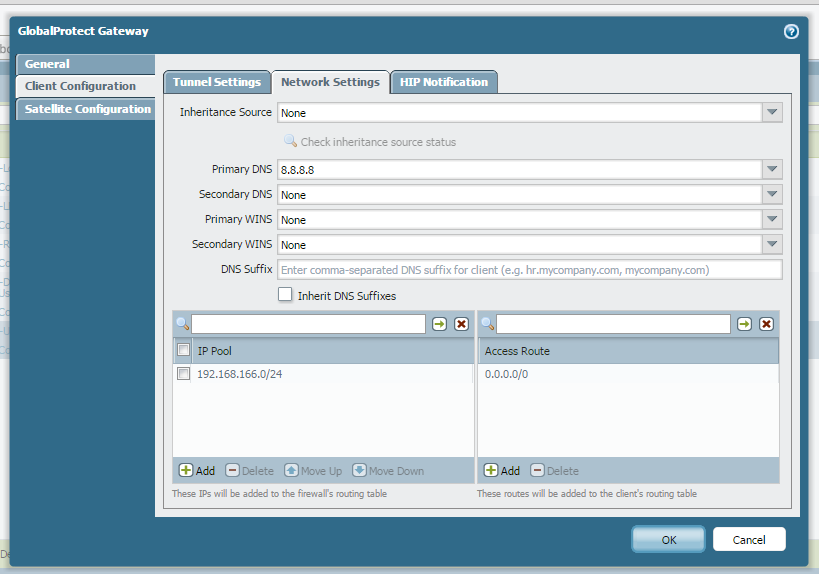
Step 7. Configure Gateway:
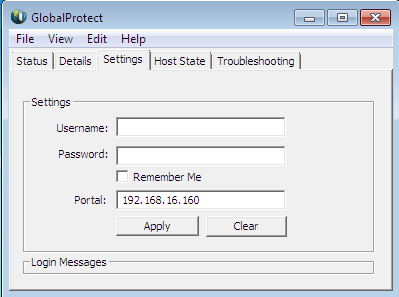
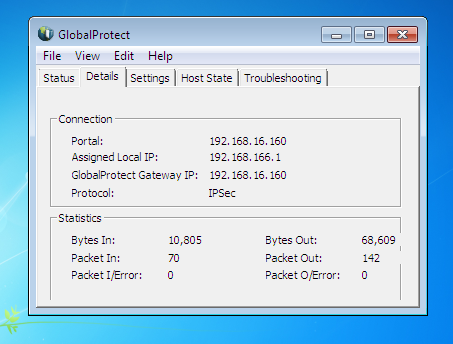
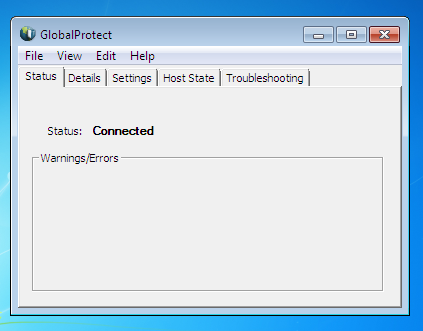
Step 8. Log in to the Windows machine with domain credentials, install the client certificate on the machine, and enter only the IP address of the portal.