Correct Group and IP to User Mapping in Multi-domain AD Forest using Global Catalog
Resolution
Overview
The Global Catalog is a distributed data repository with a partial representation of every object in every domain in a multi-domain Active Directory Domain forest. This is why it is useful for the Palo Alto Networks firewall to have access to the Global Catalog. This eliminates the need for the firewall to connect to all the DC's in the forest, and it will maintain only one connection to an external resource. That connection will be on port 3268 or 3269 if it is SSL.
Details
When multiple domains are in use, sometimes there is a struggle to get the correct group and IP to user mapping on the firewall. To be more precise, sometimes besides the user behind the IP address being known, the domain information on the firewall can be wrong. This will cause the traffic for that user to match the wrong security rule.
To get past this problem, connect to the Global Catalog and establish multiple connections to it, making sure to override the domain and have the correct base.
For this scenario, there are 3 different domains connected in the same forest using the Global Catalog connection. The domain names are: il.al.com, pub.al.com and mk.al.com, which are all subdomains of al.com.
In each connection, it is connected using the same Bind DN (a user in the root domain, that has rights to read the information in the subdomains), but will connect to a different base and override the domain information accordingly.
- For the "il.al.com" domain: the Base is "DC=il,DC=al,DC=com" and the domain is "il"
- For the "pub.al.com" domain: the Base is "DC=pub,DC=al,DC=com" and the domain is "pub"
- For the "mk.al.com" domain: the Base is "DC=mk,DC=al,DC=com" and the domain is "mk"
Configure these changes under, Device > Server Profiles > LDAP:

This configuration allows the firewall to fetch the needed group mappings for each domain and append the domain in front, so it has the correct user and group information and the correct policy is in use.
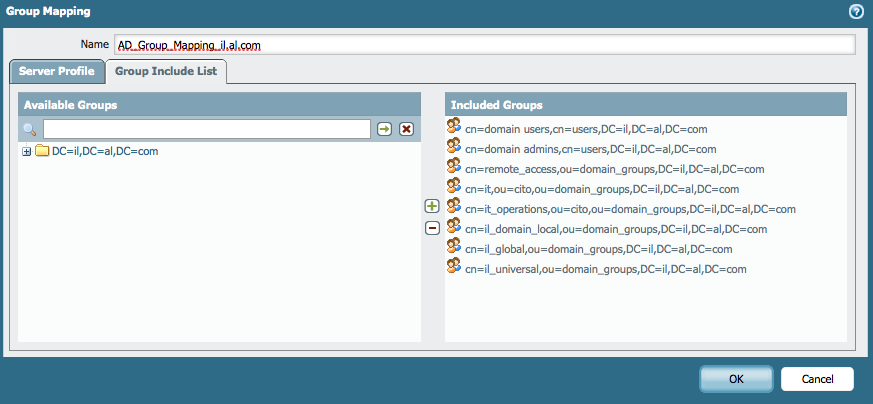
Configure the Group Mapping Setting under, Device > User Identification > Group Mapping Setting, to use the newly created Server Profile.

As shown below, add Group Filters if needed:
See Also
How to Configure Group-Mapping in a Multi-Domain Active Directory Domain Services (AD DS) Forest
owner: ialeksov