Here is a document to configure ECMP enabled OSPF over IPSec VPN. This document explains about the advertisement of a single route over two IPSec tunnels with ECMP enabled. In this case, there is a loopback interface used; however, any routes can be advertised following these steps.
For this documentation purpose, here is the topology for your reference:
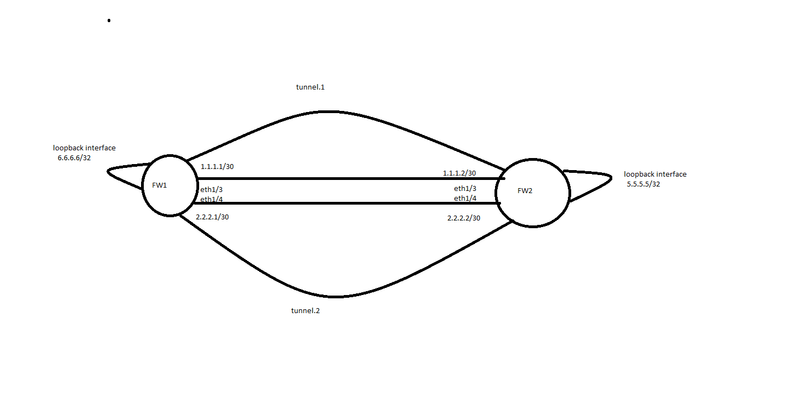
The basic configuration of dual ISP and IPsec VPN is not discussed in this article.
Please note: Both the routes if present in the routing table, only one will be seen in the forwarding table unless and until you enable ECMP on the interfaces.
Prerequisites
1) Two interfaces having the public ISP.
2) Ipsec VPN established across both ISP's.
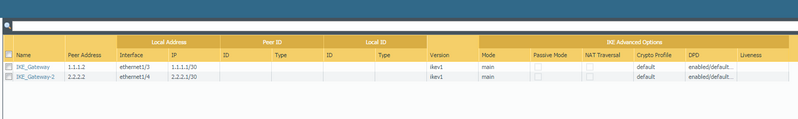
Here is the configuration details for FW1:
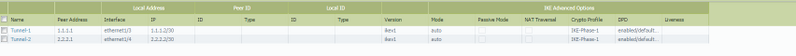
IPsec Tunnels will look like this:
##Phase 1 settings of the Ipsec VPN:
##Phase 2 settings of the IPSec VPN:

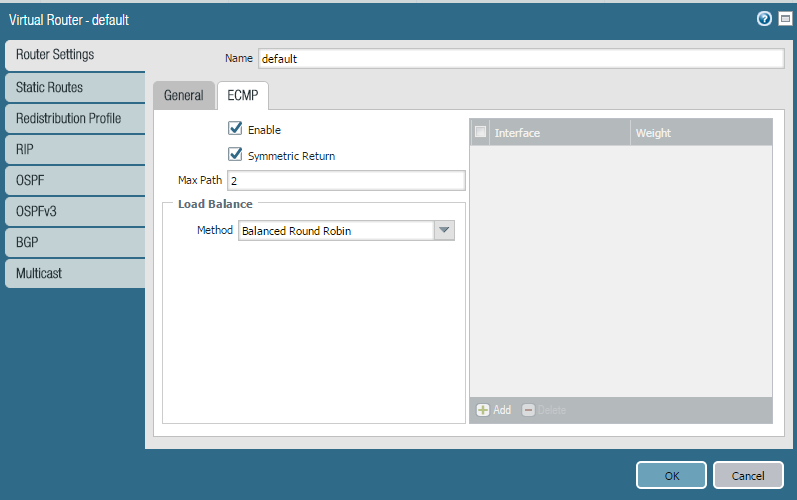
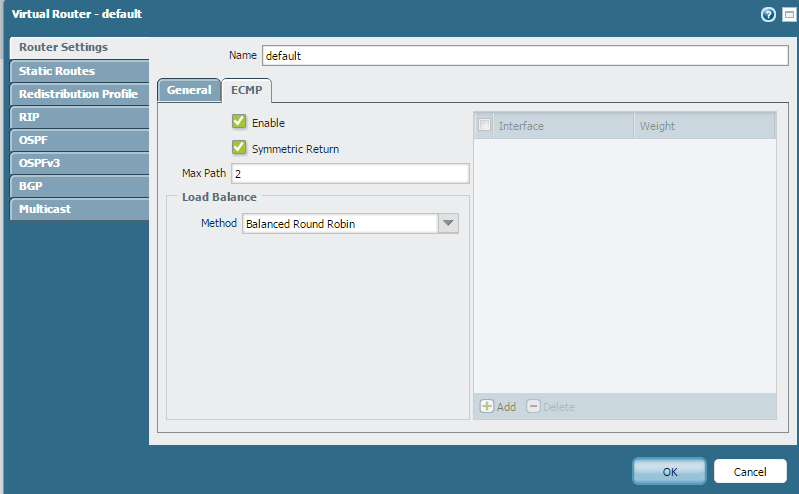
## Virtual Router settings:
1) Navigate to Network>Virtual router> Router Settings
2) Enable ECMP and symmetric return.
3) You can select the Load Balance method as per your requirement.
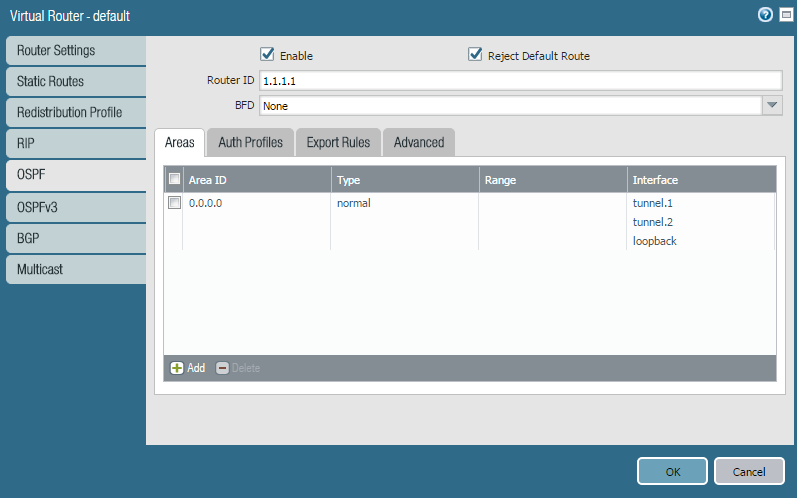
4) OSPF configuration:
a) Network>Virtual router>Select the virtual router>OSPF
b) Enable OSPF
c) Assign a router ID.
d) Click on area tab, then click add.
e) Give an area ID and assign the interfaces that needs to be a part of OSPF.
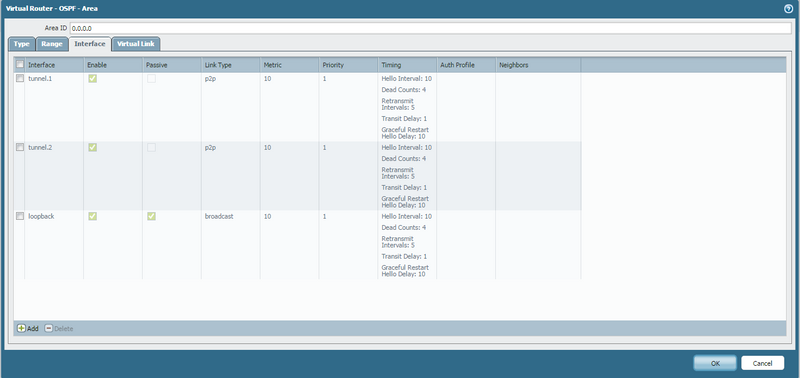
f) Configuration of Interfaces in OSPF:
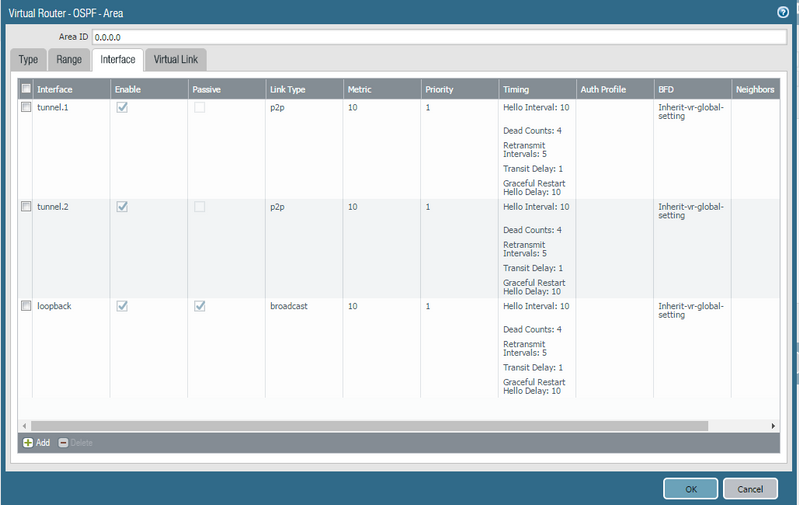
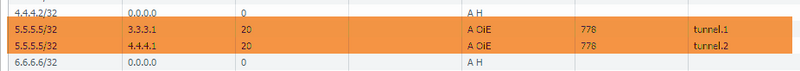
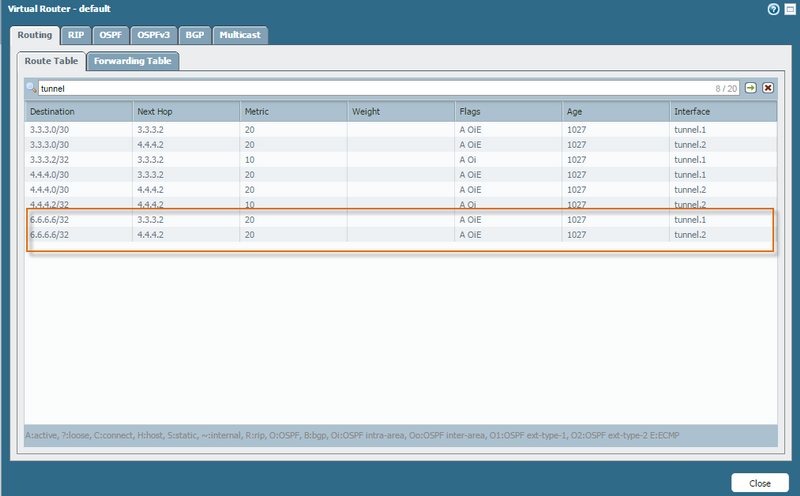
After performing the configuration ,the Runtime statistics will be seen as follows:
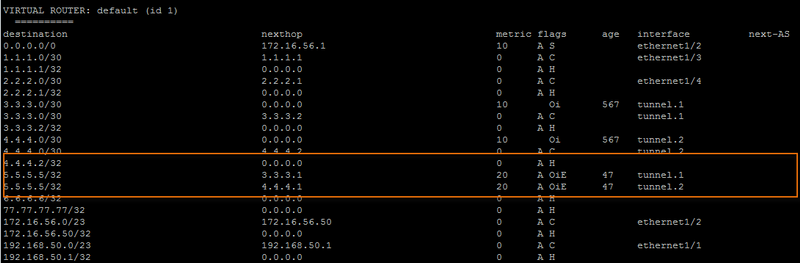
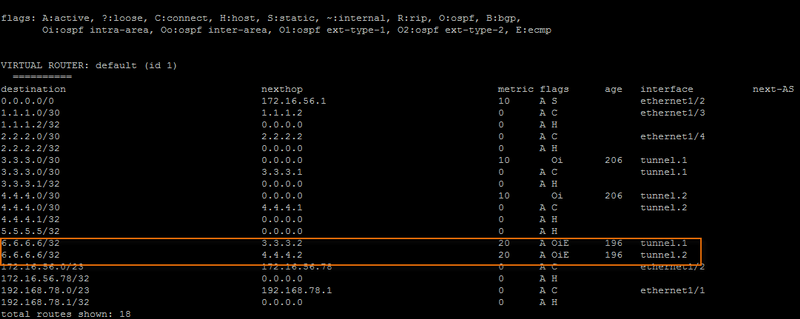
From the CLI, the output of the route distributed via ECMP OSPF will be seen as folows:
Similarly, the configuration for FW2 remains same.
Please find the attached snapshots of the configuration for FW2:
IKE configuration FW2
IPsec Configuration FW2

VIrtual Router configuration:
VIrtual Router OSPF configuration: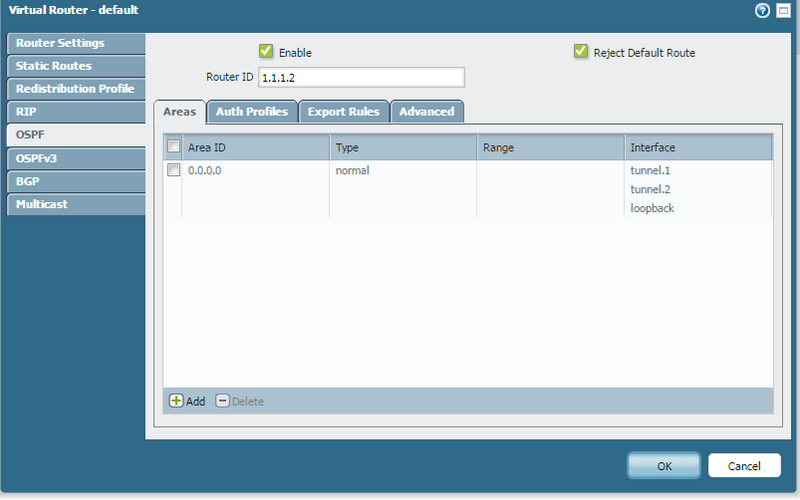
The output of the routing table in runtime statistics will be seen as follows:
From the CLI, the routing table will be seen as follows:
Here are a few related documents for your reference:
https://live.paloaltonetworks.com/t5/Configuration-Articles/How-to-Configure-Dual-VPNs-with-Dual-ISPs-from-a-Single-Firewall/ta-p/60842
https://live.paloaltonetworks.com/t5/Configuration-Articles/How-to-Configure-IPSec-VPN/ta-p/56535
https://live.paloaltonetworks.com/t5/Configuration-Articles/How-to-Configure-a-Palo-Alto-Networks-Firewall-with-Dual-ISPs/ta-p/59774
https://live.paloaltonetworks.com/t5/Tech-Note-Articles/How-to-Configure-Dynamic-Routing-over-IPSec-against-Cisco/ta-p/60523