Overview
PAN-OS 6.0 introduced the ability to use the Palo Alto Networks firewall and the User-ID Agent as a syslog listener for collecting syslogs from different systems in the network, and to map users to IP addresses. The user to IP mappings could be used in security rules and policies. The version of PAN-OS on the firewall and the version of the User-ID Agent should be at least 6.0.
Note: The version of PAN-OS on the firewall should be the same or higher than the version of User-ID Agent, but preferably the same.
This document describes how to configure a custom syslog sender on the User-ID Agent installed on a Windows server. For a similar configuration on the Palo Alto Networks firewall, see: How to Configure a Custom Syslog Sender and Test User Mappings.
While the firewall has the ability to use predefine filters as a syslog sender on the User-ID agent, the administrator needs to create filters depending on the logs generated by the network system. As a prerequisite to this configuration, it is assumed that the User-ID Agent is connected to the firewall and the user-ip-mappings have been sent to the connected Palo Alto Networks devices.
Additional requirements:
- Knowledge of the syslog sender logs
- Knowledge of the IP address of the sender
- Knowledge of available ports on the server that can be used for accepting the logs
- Knowledge of the domain on which the users are connecting and if using a “domain\” notation when logging in
- Decision between using a Field Identifier or a Regex Identifier
Steps
Analysis of the logs:
Take a section of the log and try to find the needed fields for user-ip mapping. These fields need to include; the username, the IP address, the delimiters and the 'Event String'. The event string will tell the firewall that a specific user is successfully logged in and that it needs to collect the username and the IP address, and add them in the user-ip-mappings database.
The following syslog example shows a log from an Aruba wireless controller:
2013-03-20 12:56:53 local4.notice Aruba-Local3 authmgr[1568]: <522008> <NOTI> <Aruba-Local3 10.200.10.10> User Authentication Successful: username=ilija MAC=78:f5:fd:dd:ff:90 IP=10.200.27.67
2013-03-20 12:56:53 local4.notice Aruba-Local3 authmgr[1568]: <522008> <NOTI> <Aruba-Local3 10.200.10.10> User Authentication Successful: username=jovan MAC=78:f5:fd:dd:ff:90 IP=10.200.27.68 role=MUST-STAFF_UR VLAN=472 AP=00:1a:1e:c5:13:c0 SSID=MUST-DOT1X AAA profile=MUST-DOT1X_AAAP auth method=802.1x auth server=STAFF
2013-03-20 12:56:57 local4.notice Aruba-Local3 authmgr[1568]: <522008> <NOTI> <Aruba-Local3 10.200.10.10> User Authentication Successful: username=1209853ab111018 MAC=c0:9f:42:b4:c5:78 IP=10.200.36.176 role=Guest VLAN=436 AP=00:1a:1e:c5:13:ee SSID=Guest AAA profile=Guest auth method=Web auth server=Guest
2013-03-20 12:57:13 local4.notice Aruba-Local3 authmgr[1568]: <522008> <NOTI> <Aruba-Local3 10.200.10.10> User Authentication Successful: username=1109853ab111008 MAC=00:88:65:c4:13:55 IP=10.200.40.201 role=Guest VLAN=440 AP=00:1a:1e:c5:ed:11 SSID=Guest AAA profile=Guest auth method=Web auth server=Guest
From the analysis of the above log sample (a syslog output), the parsing can be handled using Filed Identifiers.
- As a Event String search for the 'User Authentication Successful' string
- As a username prefix use: 'username='
- As a username delimiter: 'empty space'
- As an address prefix: 'IP='
- As an address delimiter: 'empty space'
NOTE: 'Empty space' means using the space button on the keyboard.
Configuration:
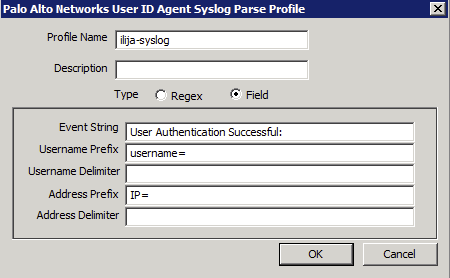
- Define the Syslog Parser Profile, which will be used for the Syslog events that are sent to the firewalls listener.
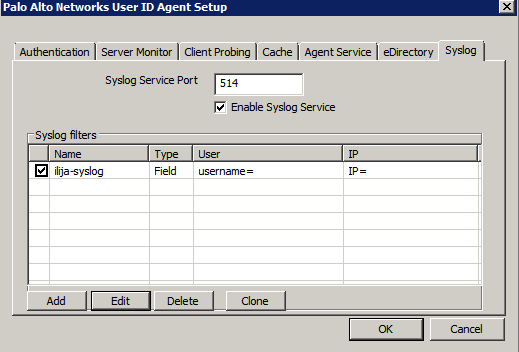
- On the User-ID Agent go under: Setup > Edit > Syslog
- Select the port to listen for new syslog messages
- Add a new Syslog Parser Profile
- Add appropriate Profile Name and Description (if needed)
- Select the appropriate Type of parser (the Field Identifier is configured in this example)
- Enter the details as determent from the analysis done before
- Do not forget to enable the Syslog Service
The fully configured syslog filter should look like this:
- Configure the server in the list of monitored servers:
- Go to User ID > Discovery, and add a new server
- Enter the Name the IP address and choose the syslog sender as a Server Type
- Add a Filter select, the filter that was defined in the previous step
- Add a Default Domain Name if needed, (if this is added, the domain field be prepended to all of the users that are discovered using this server connection)
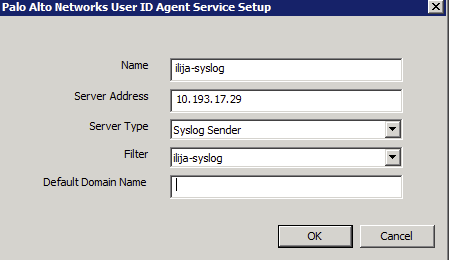
- Commit the changes to the User-ID Agent
- Confirm that the server is listening on the defined port (use the 'netstat' command in the cmd on the server)
- Check if receiving the logs from the server sender and generating the mapping on the User-ID Agent
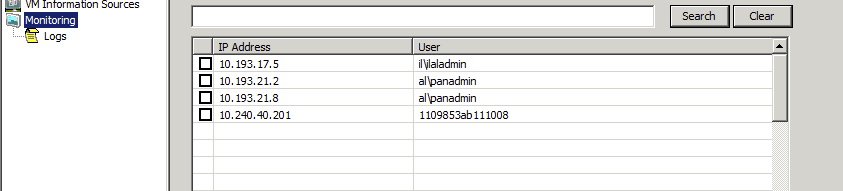
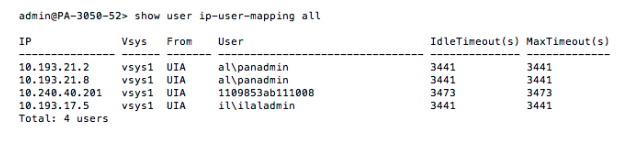
- On the firewall, check to see if receiving the mappings from the User-ID Agent. These mappings will be User-ID Agent type, because they were collected from the User-ID Agent and given to the firewall.
owner: ialeksov