How to Deal with Conficker using DNS Sinkhole
Procedure
PAN-OS 6.0, 6.1
Overview
Conficker was first detected in November 2008, and is one of the most widespread worms that infects machines running Windows OS. Palo Alto Networks has created signatures that can detect and block the Conficker worm. Among them are Anti-Virus/Anti-Spyware signatures that detect the DNS domains used by Conficker variants. These domains are updated as soon as Conficker variants are discovered. If a WildFire license is used, the newly discovered domains are pushed to the Palo Alto Networks firewall every hour through the WildFire signatures. If a license is not used, the signatures are pushed every 24 hours and downloaded by dynamic updates to for all Palo Alto Networks devices. Updates will also be implemented in the new AV signatures in the next update interval. This protection detects when a user in the network is requesting “bad” domains. When an analysis of the logs is completed, it can be reviewed and determined that the request for the infected domain came from the local DNS server. This is possible because of the hierarchical nature of DNS.
Details
All Palo Alto Networks platforms have an implementation of sinkhole action for queries towards malicious domains. Using this capability, the Palo Alto Networks firewall can detect the infected host in the network and send notification to the security administrator. This enables the infected workstation to be removed from the network.
How it works:
- The infected machine asks for a DNS resolution of an infected domain from the local DNS server.
- The local DNS forwards the query to the public DNS server.
- The Palo Alto Networks device sees the query and detects the malicious domain using the newest signatures.
- It overrides the DNS response with an IP address that the administrator dedicates, (sinkhole address) and sends the spoofed response to the client.
- The client attempts a connection to the sinkhole IP address.
- The Palo Alto Networks blocks the traffic and logs the attempt.
- The firewall administrator receives a notification about the event.
- The malicious client is removed from the network and cleaned.
Steps
To configure the DNS sinkhole action, see: How to Configure DNS Sinkholing on PAN-OS 6.0
Using a Palo Alto Networks device that is dedicated to an L3 interface as a sinkhole interface, (the loopback interface can be used) perform the following steps:
- Add the interface to a virtual router and to a security zone, as shown in the example. This zone is different because it is where users are initiating connections. A best practice is to create a new sinkhole zone for this interface, as it is never certain where the malicious machines will send traffic.
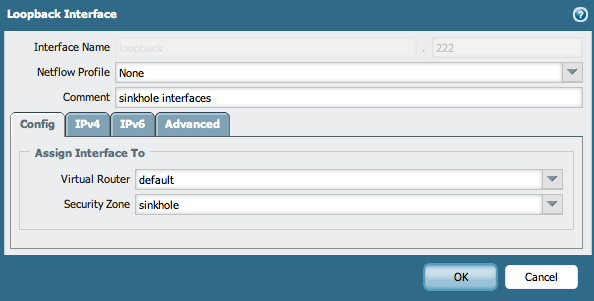
The creation of the new "sinkhole" zone places the created loopback interface as loopback.222.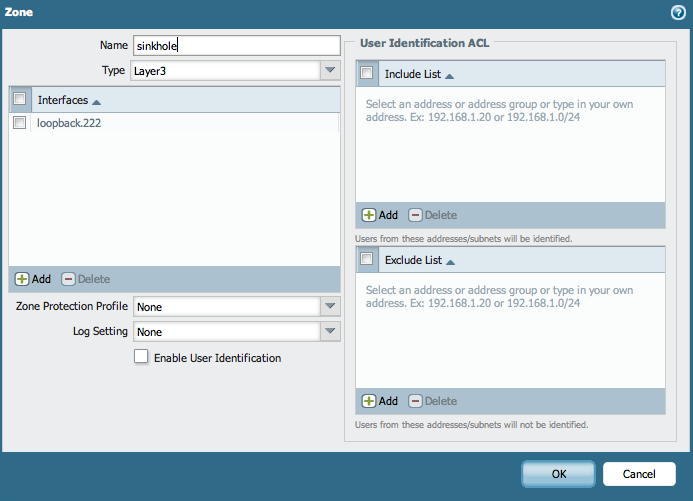
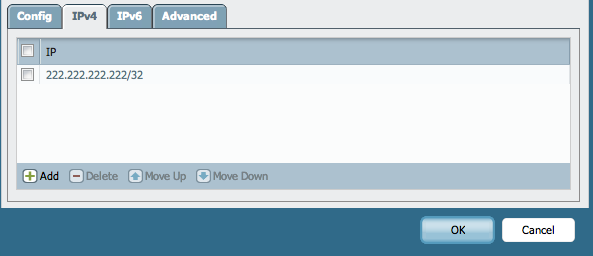
- Add an IP address to the interface that is not currently being used and that is well known to the administrator.
- If IPv6 is used throughout the company, also assign an IPv6 address to the interface.
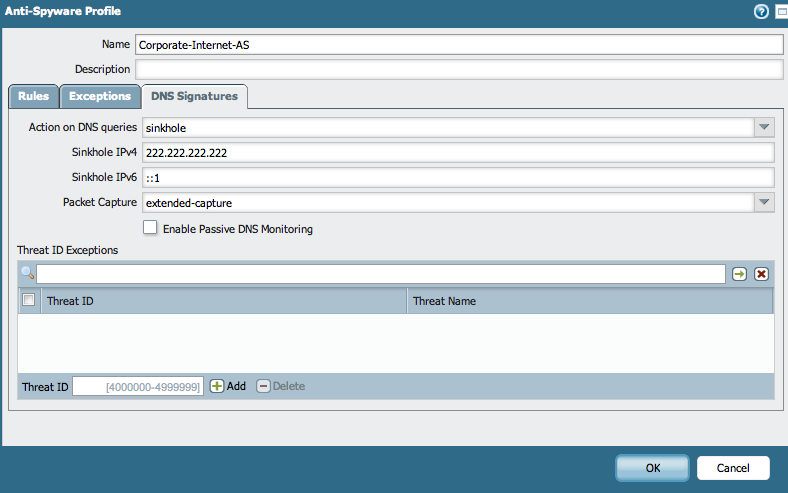
- Go to Objects > Security Profiles > Anti-Spyware, choose (or create) the Profile that will be assigned to the internet user.
- Under DNS Signatures, select sinkhole as an action on DNS queries. If block is chosen, it will block the queries to the malicious domains. In the logs, only the local DNS will be shown as an attacker. Choose the sinkhole IP address that was generated before (222.222.222.222). Choose the IPv6 IP address for the IPv6 DNS queries.
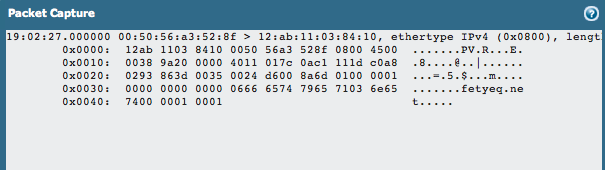
- Select extended-capture in packet capture to allow more packets to be captured than only the one that triggered the signature. This value is defined under Device > Setup > Content-ID > Threat Detection Settings.
- Apply the Anti-Spyware Profile to a security rule and enable log at session end.
- Commit the configuration.
Testing
After the configuration is complete, validate if the traffic is captured and identify the malicious workstation.
- Open a test machine behind the firewall.
- Initiate DNS traffic for one of the Conficker domains (for this test fetyeq.net will be used).
Note: To check for more Conficker domains, open the Antivirus Release Notes of the dynamic updates that have been installed on the Palo Alto Networks devices. Palo Alto Networks updates these domains on a regular basis and they can be found in the Release Notes for the Antivirus signatures. - Go to Devices > Dynamic-Updates > Antivirus > Release Notes and search for “conficker." There should be around 1,000 domains to review.
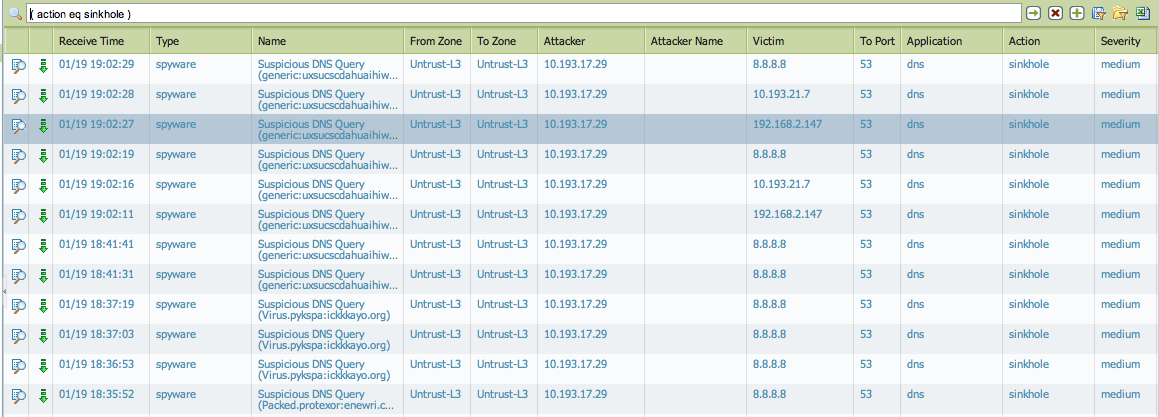
- Check the threat logs for any logs with action sinkhole.
- If needed, check the packet capture.
- Generate a custom report using the "sinkhole action" as a filter in the query builder and schedule it to run daily.
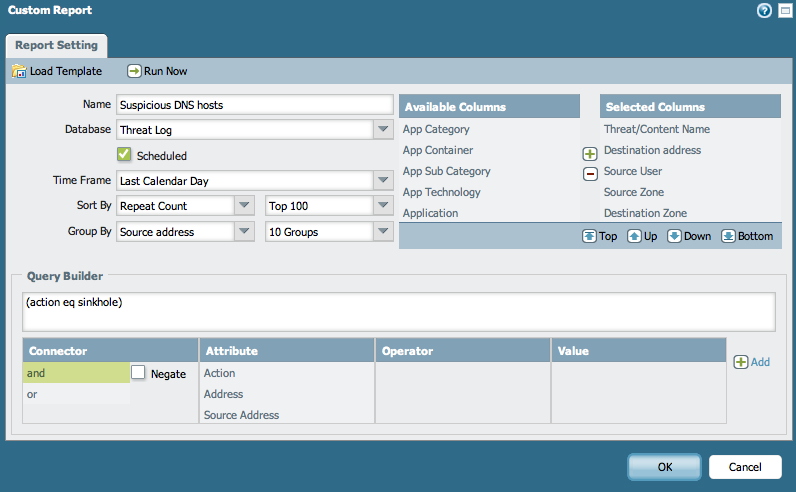
- Check the report the following day to confirm it's collecting and displaying data.
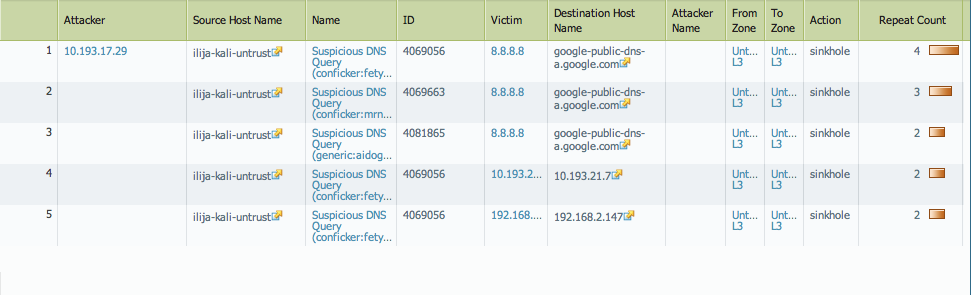
Following the steps above tracks and isolates malicious workstations in the designated network.
owner: ialeksov