User-ID is a key component in any sucsessful Palo Alto Networks offering or solution. Palo Alto Networks improves the way User-ID works in PAN-OS 7.1 through three key enhancements:
- User-ID redistribution
- User-ID configurable Ignore User List
- User-ID Group Capacity Increase
User-ID redistribution
Issue
On PAN-OS 7.0, a firewall that receives IP/user mappings from a redistributing firewall cannot redistribute them further.
Users with complex User-ID topologies have a need for multihop User-ID information redistribution.
Solution
Using Palo Alto Networks firewalls running PAN-OS 7.1 as User-ID agents, IP/user mappings can be distributed up to a depth of 10 levels.
Description
Redistribution agents can receive IP/user mappings from all available sources of User-ID information, including Windows UID agents, GlobalProtect, Captive Portal, XML API, Syslog and server monitoring. Firewall agents flagged as distribution points aggregate User-ID data from multiple upstream firewall agents and resolve any conflicting User-ID mappings from these agents.
Limitations
- A given IP/user mapping is redistributable to a maximum of 10 hops from the source that originally learned this IP/user mapping.
- A maximum of 100 agents is configurable as User-ID agents per platform on all PAN-OS platforms.
- Redistribution components that are out-of-scope for this feature:
- Redistribution of LDAP groups (workaround: use LDAP Proxy)
- Redistribution of Terminal Services information
- Use of Windows UID agents as redistribution points
- Use of Panorama as a redistribution point
- Redistribution of HIP
Configuration
User-ID redistribution is configured using the existing User-ID configuration option.
The example shows a firewall in the middle of a redistribution chain.
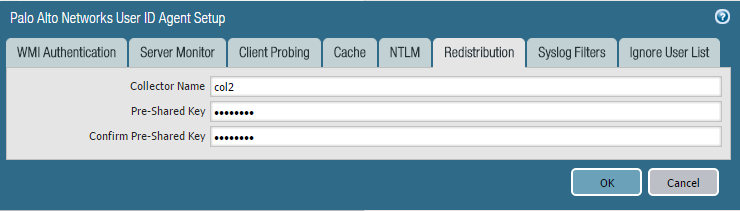
Inside Device > User Identification > User Mapping, click the sprocket icon in the upper right to get to this window:
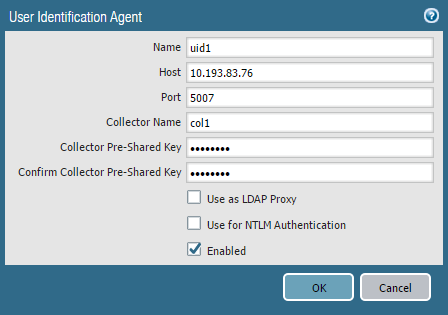
Inside Device > User Identification > User-ID Agents, click 'Add' for a new agent, or click on an existing agent.
Downgrade
On downgrade of PAN-OS, configuration stays in place but IP/user mappings cannot be distributed more than one hop in 7.0 or earlier releases. Any configured redistribution options will effectively be ignored in such a scenario.
User-ID configurable Ignore User List
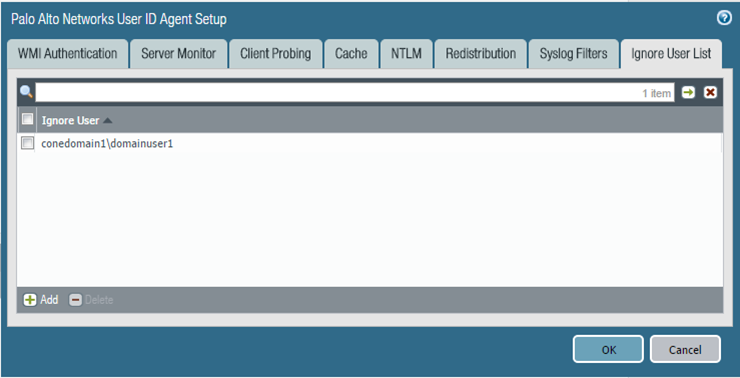
A new tab, ‘Ignore User List’ is added in the Device > User Identification > Palo Alto Netoworks User ID Agent Setup configuration section.
Wildcards are supported at the end of the input so, for example, conedomain1\dom* covers conedomain1\domainuser, conedomain1\domainadmin, etc.
User-ID group capacity increase on PA-5060, PA-7050 and PA-7080
Issue
Networks that are evolving towards a zero trust model often require vast numbers of user groups, each of which generally signifies a network resource or an application.
Currently only 640 groups are configurable in polices.
Solution
Allow configuration of up to 3,200 groups within any User-ID aware policy construct on the PA-5060, PA-7050 and PA-7080 platforms when those platforms are being used in a single vsys mode.
- Increase is only configurable when the device is functioning in a single-vsys mode. If multiple virtual systems are enabled, User-ID falls back to 640 groups per vsys.
- Increase is applicable to Security, QoS, Decryption and Captive Portal polices.
If a PAN-OS 7.1 device is configured with more than 640 groups when in single vsys mode, and an administrator makes a configuration change to enable multiple virtual systems, the command fails.
Downgrade
If a downgrade is requested from PAN-OS 7.1 and the configuration carries more than 640 groups, the downgrade request stops with an error.
Panorama
Configuration push from Panorama to devices that do not support more than 640 groups fails.