Create a Firewall on AzureRM via Azure PowerShell
Resolution
Aim
Create a Palo Alto Networks Next-Generation firewall with 4 interfaces (management, untrust, trust, DMZ) using Azure PowerShell. Make sure Azure PowerShell commandlets are installed. Installing them using Microsoft Web Platform Installer is an easy approach and the following procedure link can help more.
Procedure
Step 1: Create Resource Group
- Login to Azure using your credentials - "Login-AzureRmAccount". A successful login will display account info.
- Set location variable: $location = 'East US'
- Create resource group: New-AzureRmResourceGroup -ResourceGroupName "stumuluri-rg" -Location $location
- $rg = "stumuluri-rg"
Step 2: Set up Network Security Group (NSG)
Azure NSG controls inbound and outbound traffic for assigned VMs and interface. In the following example, I am allowing everything inbound. It is not recommended for production firewalls. It is highly recommended to restrict to ports needed. Also, it is highly recommended to use different NSGs for mgmt, untrust and common NSG for trust and other internal zones. The following example is suited for internal zones where all traffic is routed to the firewall and has no Internet access.
- Creating ACL for NSG: $nsgrule = New-AzureRmNetworkSecurityRuleConfig -Name "Inbound-test" -Direction Inbound -Protocol * -SourcePortRange * -SourceAddressPrefix * -DestinationPortRange * -DestinationAddressPrefix * -Priority "100" -Access Allow -Description "allow_all"
- Creating NSG: $nsg = New-AzureRmNetworkSecurityGroup -ResourceGroupName $rg -Location $location -Name "allow_all_nsg" -SecurityRules $nsgrule
Step 3: Set up Network Infrastructure information
Setting up network information includes creating network subnets, interfaces, public IP that can be assigned to firewall later in process
- Create Subnets:
- $mgmtconfig = New-AzureRmVirtualNetworkSubnetConfig -Name "stumuluri-mgmt" -AddressPrefix "10.55.0.0/24" -NetworkSecurityGroup $nsg
- $untrustconfig = New-AzureRmVirtualNetworkSubnetConfig -Name "stumuluri-untrust" -AddressPrefix "10.55.1.0/24" -NetworkSecurityGroup $nsg
- $trustconfig = New-AzureRmVirtualNetworkSubnetConfig -Name "stumuluri-trust" -AddressPrefix "10.55.2.0/24" -NetworkSecurityGroup $nsg
- $dmzconfig = New-AzureRmVirtualNetworkSubnetConfig -Name "stumuluri-dmz" -AddressPrefix "10.55.3.0/24" -NetworkSecurityGroup $nsg
- Create Virtual network (VNet):
- $vnetname = 'stumuluri-virtN'
- $vnet = New-AzureRmVirtualNetwork -Name 'stumuluri-virtN' -ResourceGroupName $rg -Location $location -AddressPrefix 10.55.0.0/16 -Subnet $mgmtconfig,$untrustconfig,$trustconfig,$dmzconfig
- Get Public IPs:
- $mpip = New-AzureRmPublicIpAddress -ResourceGroupName $rg -Location $location -AllocationMethod Static -Name 'mymgmtip' -DomainNameLabel 'stumuluri-mgmt'
- $upip = New-AzureRmPublicIpAddress -ResourceGroupName $rg -Location $location -AllocationMethod Static -Name 'myuntrustip' -DomainNameLabel 'stumuluri-mgmt2'
- Create Interfaces: Creating network interfaces and assigning a subnets requires to know the subnet id provided for the subnet inside VNet. To get this get id see the info that is assigned to $vnet in above step
- $vnet (Subnet ID start from 0)
- $mgmt_nic = New-AzureRmNetworkInterface -ResourceGroupName $rg -Location $location -Name 'stumuluri-fw-mgmt' -SubnetId $vnet.Subnets[0].Id -PublicIpAddressId $mpip.Id -PrivateIpAddress 10.55.0.4 -EnableIPForwarding
- $untrust_nic = New-AzureRmNetworkInterface -ResourceGroupName $rg -Location $location -Name 'stumuluri-fw-untrust' -SubnetId $vnet.Subnets[1].Id -PublicIpAddressId $upip.Id -PrivateIpAddress 10.55.1.4 -EnableIPForwarding
- $trust_nic = New-AzureRmNetworkInterface -ResourceGroupName $rg -Location $location -Name 'stumuluri-fw-trust' -SubnetId $vnet.Subnets[2].Id -PrivateIpAddress 10.55.2.4 -EnableIPForwarding
- $dmz_nic = New-AzureRmNetworkInterface -ResourceGroupName $rg -Location $location -Name 'stumuluri-fw-dmz' -SubnetId $vnet.Subnets[3].Id -PrivateIpAddress 10.55.3.4 -EnableIPForwarding
Step 4: Build PANW NSG-FW
- PAN-OS Properties: Run the following commands to define the PAN OS Version
- $publisher = 'paloaltonetworks'
- $offer = 'vmseries1'
- $sku = 'byol' (Can be byol or bundle1 or bundle2 ; Reference 1 ; Reference 2 ; admin guide)
- $version = 'latest' (Can be versions 8.0.0. 7.1.1 or latest)
- $size ='Standard_D3_v2' (refer the section of "Minimum System Requirements for the VM-Series on Azure" for different sizes in admin guide)
- Get Credentials: Alternatively, you can user New-Object to directly type password to command or public key
- $cred = Get-Credential
- $sshkey = '<public-key'
- $username ='stumuluri'
- Define VM: $fvm = New-AzureRmVMConfig -VMName 'stumuluri-nsg-fw' -VMSize $size
- Storage Account: Sku for storage accounts has multiple variations and can be found here
- $saccount = New-AzureRmStorageAccount -StorageAccountName 'stumulurist' -Location $location -ResourceGroupName $rg -SkuName Standard_LRS
- Operating System Info: $fvm = Set-AzureRmVMOperatingSystem -VM $fvm -Linux -ComputerName 'stumuluri-fw' -Credential $cred
- Assign PAN-OS to VM: $fvm = Set-AzureRmVMSourceImage -VM $fvm -PublisherName $publisher -Offer $offer -Skus $sku -Version $version
- Storage: $fvm = Set-AzureRmVMOSDisk -vm $fvm -Name 'panosdisk' -DiskSizeInGB 60 -CreateOption FromImage -Caching ReadWrite -StorageAccountType StandardLRS -Linux
- Pricing: $fvm = Set-AzureRmVMPlan -VM $fvm -Publisher $publisher -Name $sku -Product $offer
- Interfaces:
- $fvm = Add-AzureRmVMNetworkInterface -VM $fvm -Id $mgmt_nic.Id -Primary
- $fvm = Add-AzureRmVMNetworkInterface -VM $fvm -Id $untrust_nic.Id
- $fvm = Add-AzureRmVMNetworkInterface -VM $fvm -Id $dmz_nic.Id
- $fvm = Add-AzureRmVMNetworkInterface -VM $fvm -Id $trust_nic.Id
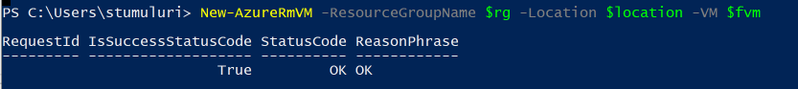
- Initialize VM: New-AzureRmVM -ResourceGroupName $rg -Location $location -VM $fvm
 Step 5: Set up routing defaulting to PANW-FW on Trust and DMZ
Step 5: Set up routing defaulting to PANW-FW on Trust and DMZ
- Adding default routes:
- $troute = New-AzureRmRouteConfig -Name default -AddressPrefix 0.0.0.0/0 -NextHopType VirtualAppliance -NextHopIpAddress 10.55.2.4
- $droute = New-AzureRmRouteConfig -Name default -AddressPrefix 0.0.0.0/0 -NextHopType VirtualAppliance -NextHopIpAddress 10.55.3.4
- $uroute = New-AzureRmRouteConfig -Name default -AddressPrefix 0.0.0.0/0 -NextHopType Internet
- Creating routing table:
- $trustroutingtable = New-AzureRmRouteTable -ResourceGroupName $rg -Location $location -Name "stumuluri-trust" -Route $troute
- $dmzroutingtable = New-AzureRmRouteTable -ResourceGroupName $rg -Location $location -Name "stumuluri-dmz" -Route $droute
- $untrustroutingtable = New-AzureRmRouteTable -ResourceGroupName $rg -Location $location -Name "stumuluri-untrust" -Route $uroute
- Update Subnets with Routing table:
- $dmsub = $vnet.Subnets[3]
- $vnet = Set-AzureRmVirtualNetworkSubnetConfig -VirtualNetwork $vnet -Name $dmsub.Name -AddressPrefix $dmsub.AddressPrefix -NetworkSecurityGroup $dmsub.NetworkSecurityGroup -RouteTable $dmzroutingtable
- $trust = $vnet.Subnets[2]
- $vnet = Set-AzureRmVirtualNetworkSubnetConfig -VirtualNetwork $vnet -Name $trust.Name -AddressPrefix $trust.AddressPrefix -NetworkSecurityGroup $trust.NetworkSecurityGroup -RouteTable $trustroutingtable
- $unsub = $vnet.Subnets[1]
- $vnet = = Set-AzureRmVirtualNetworkSubnetConfig -VirtualNetwork $vnet -Name $unsub.Name -AddressPrefix $unsub.AddressPrefix -NetworkSecurityGroup $unsub.NetworkSecurityGroup -RouteTable $untrustroutingtable
- Update VNET: $vnet = Set-AzureRmVirtualNetwork -VirtualNetwork $vnet
Step 6: Log in to Firewall and setup firewall config
You can configure the firewall to get IP via DHCP or use static IP. As we statically assigned IP on the Azure side for interface, it will remain the same.